News organizations love confidential tip pages. And what’s not to love? Confidential tip pages call attention to several channels for sources to reach out, and signal that news organizations take confidentiality seriously. But they can only help if someone actually reads them before reaching out. When a source who needs confidentiality reaches out over an unsecured channel, or in a situation that leaves a clear data trail, they may have burned themselves.
Most sources don’t reach out with terribly sensitive information. But sometimes they do.
Let’s say our source reaches out to share a tip with our newsroom about workplace abuse. They have an interesting tip, but they’ve emailed from their workplace, on a computer their employer owns. It probably wouldn’t take a sleuth to figure out who reached out. And of course, you could tell them how to reach out over a safer channel, but it’s very possible they’ve already given their workplace all the clues they need to know who is responsible.
We call this the “first contact problem.” The very first time someone reaches out, they need to know how to do so safely, or they’ve already created a data trail that leads directly back to them.
To get sources to reach out through the safest channels, secure tip pages need to be advertised early and often. Media organizations need to have a strategy to communicate what to do, as well as what not to do. And when they do burn themselves, we need to have a plan to ensure their story is told while keeping them as safe as possible.
(Want to create a secure tip page, or improve your existing page? Read this to get started.)
Advertise, advertise, advertise
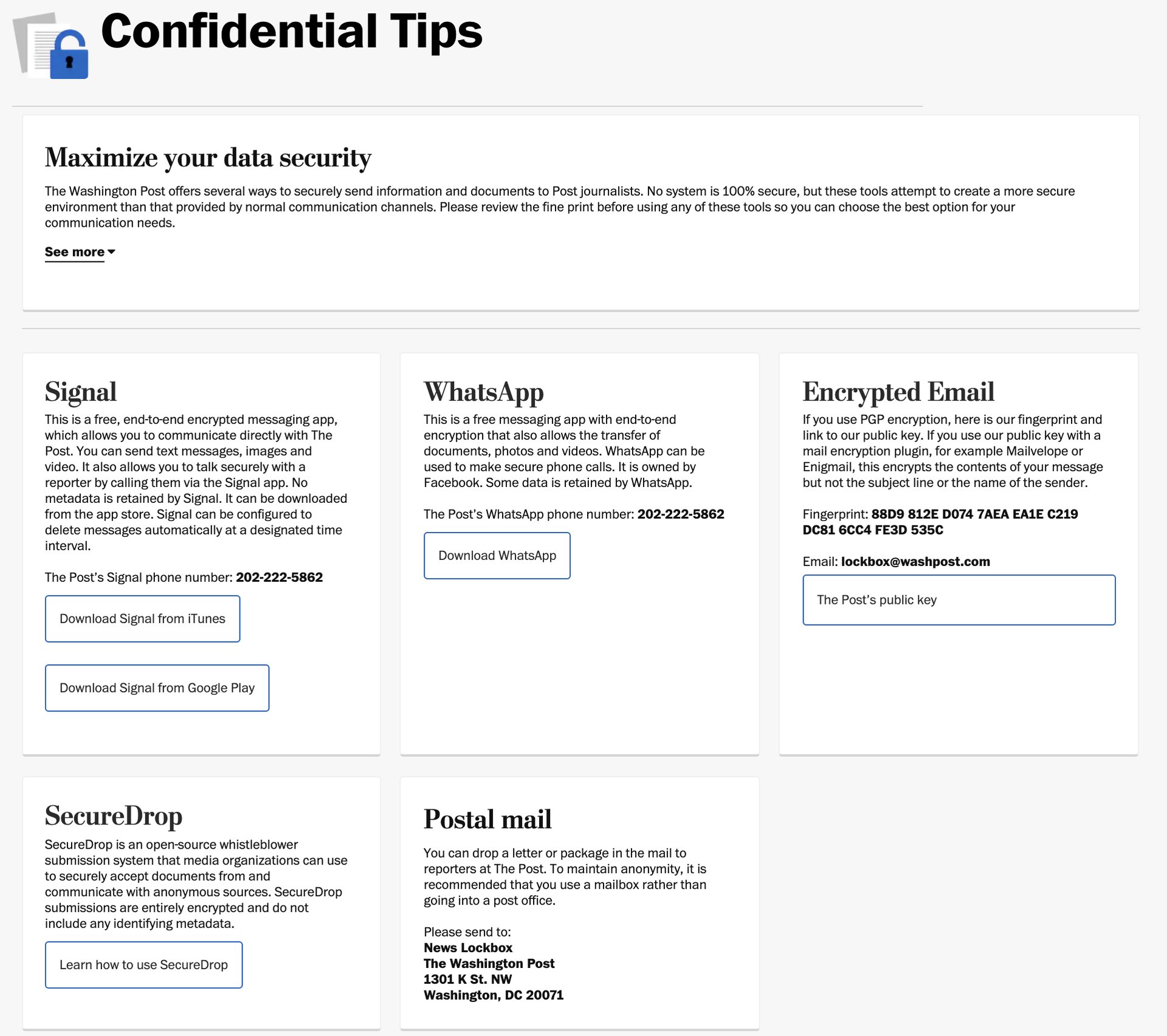
The Washington Post’s confidential tip page
A secure tip page can and should be a way to promote safer practices, but these webpages only help if sources actually read them. It sounds obvious, but the single most important thing that news organizations can do with their secure tip pages is advertise them over as many channels as possible, long before anyone plans to use them.
Sources should not have to dig through your website to get information about how to send you a tip, and no one should have to hunt this information down. Instead, anyone should be able to find this information incidentally. It should be obvious.
News organizations should post contact information for secure tip channels on all social media sites, newsletters, web forums, and in print. Individual journalists: Consider advertising your secure contact information wherever possible, and having a reliable secure contact page. (See Bart Gellman’s for inspiration.) The important part is to make sure people have the information they need to reach out before they need it. A news website’s tip page can be one of many ways to share this information.
Advertise strategies, not just tools
Put yourself in the shoes of a would-be source. What would you need to know to stay out of trouble?
Confidential tip pages often advertise encrypted tools to help fight network surveillance. This is a good start, but it’s at least as important to speak about safety strategies more broadly.
A significant part of this strategy needs to focus on what not to do.
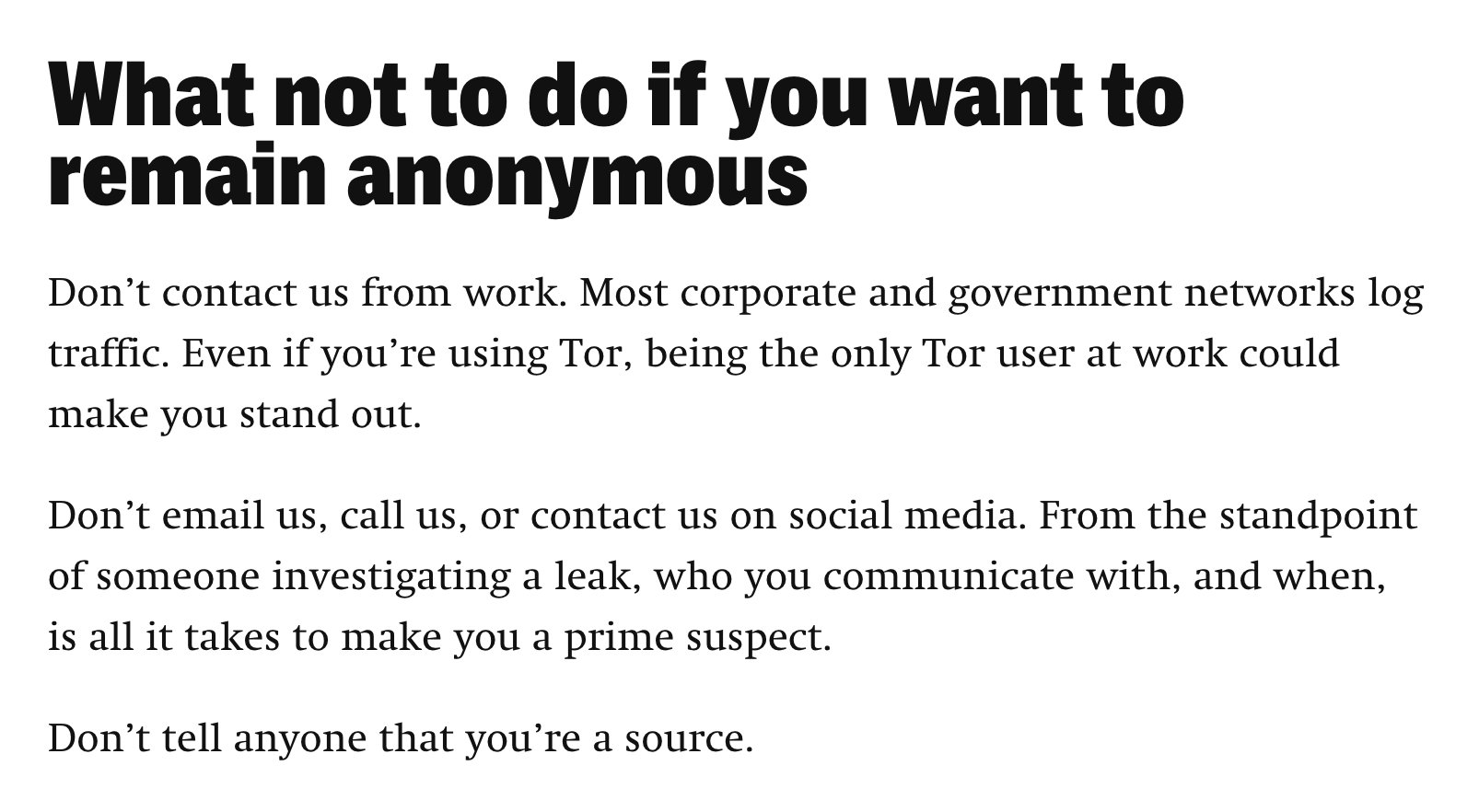
A section from the “The Intercept Welcomes Whistleblowers” tip page.
For example, The Intercept offers an excellent resource geared to anonymous whistleblowers. This is meaningful advice for anyone who wants to protect themselves from being identified by their workplace, no matter how sensitive their tips may or may not be.
We could get into the weeds thinking about the capabilities of their workplace, but we don’t want our advice to intimidate anyone, no matter their background. The Intercept keeps it simple:
- If you’re concerned about retaliation, don’t reach out from your office, or through any communication channel your workplace can access (e.g., work email, phone calls, or social media).
- Don’t tell anyone that you’re a source.
Any news organization with a tip page should consider adding this advice as well.
When sources burn themselves
So let’s fast forward.
You’ve been doing all of the right things. You’re aggressively advertising your confidential tip page with all of the right channels, and telling sources how not to reach out. At last, more internet strangers are reaching out over secure channels, and in less risky situations than ever before. Good for them, and good for you! But even still, we know people who need confidentiality will reach out in risky situations.
What now?
Reporters should make an assessment of how likely it is that they’ve actually reached out in a risky way by asking a few questions.
- Who is likely to care about this information being shared with a news organization, or the public? (e.g., a source’s employer)
- What resources (e.g., legal, technical, financial) do they have to investigate the source of the information?
- How likely do you think that really is? (Very likely? Not at all?)
- What are the likely consequences for the source if they are discovered? (Loss of reputation? Loss of livelihood?)
Reporters need to be honest with themselves, and their sources, about risk. If a source has reached out over a risky channel (e.g., using networks the employer can access) at a minimum, they’ve created a trail between themselves and a news organization. Unfortunately there are no bulletproof solutions here.
To minimize records connecting a source with a news organization, the best thing reporters can do is connect a source with a contact at a different news institution, this time using more secure channels that give you (and sources) more control.
For example, if they are concerned about being investigated by a fairly small employer, they can use channels their employer doesn’t control, such as a personal phone. But if they are concerned about an employer with far-reaching resources for investigation, they will need to take additional steps.
When an article is published with a different news organization, it lends plausible deniability to possible sources. And while this is safer, this approach also carries risk; an investigator may nonetheless be suspicious of a source’s previous connections with any news organization whatsoever.
The first contact problem is hard, and it isn’t going away. But news organizations can make a meaningful difference by advertising secure channels, how to use them strategically, and when appropriate, connecting sources to different organizations in the safest way possible for their situation.