Photo by Zero Day Initiative.
Software updates seem like a chore, but they often contain important fixes for bugs that could otherwise compromise your security and privacy. When hackers and security researchers find these bugs, their findings are first shared with affected companies, then publicly with other developers to learn what not to do with their code.
Sometimes, the timing of these software releases coincides with conferences and events in the cybersecurity industry. One example of this is Pwn2Own, a hacking contest where web browser security is put to the test against hackers from all over the world.
Every year in Vancouver, British Columbia, in one of the many glass-and-steel towers that make up the city’s skyline, teams of hackers from around the world convene in what has become the Olympics of web browser hacking. Google’s Chrome, Mozilla’s Firefox, Apple’s Safari, and Microsoft’s Edge browsers are put under siege by teams hoping to breach their code’s security mechanisms to win cash, glory, and a safer internet for all.
Sponsored by a varied mix of cybersecurity firms, as well as some of the very companies whose browsers are being hacked, participating teams can win anywhere from $30,000 to $250,000 per successful hack, or exploit, depending on the severity of a team’s successful attack on a software system’s vulnerability.
In another, Google Chrome was hacked — “pwned” by an elaborate sequence of different, previously undiscovered exploits by a hacker only known as “Pinkie Pie” (presumably named after the character from the animated series “My Little Pony: Friendship is Magic”).
In 2019, Chrome escaped a successful attack, but Safari, then Edge, Firefox, and even the Tesla entertainment console were proven vulnerable by team Fluoroacetate (named after a pesticide used to kill invasive species).
Zero-day exploits and bug bounties
Most people experience the internet through the web, and the web through browsers. Modern web browsers are made of code, and lots of it. Within these massive and complex sets of code, there’s ample room for developers to make a mistake that negatively affects a browser’s security.
This can lead to vulnerabilities that would allow malicious code on the web to potentially infect the rest of the device, which can then be used to spy on us.
Hackers have a long history of making a show of the exploits they discover. Back in 2005, when Las Vegas was still wild, hackers would demonstrate an exploit live on stage, marking the first day in which that previously undiscovered “zero-day” exploit was made known. This process sometimes led to a few arrests and subsequent “CiscoGate” T-shirt sales.
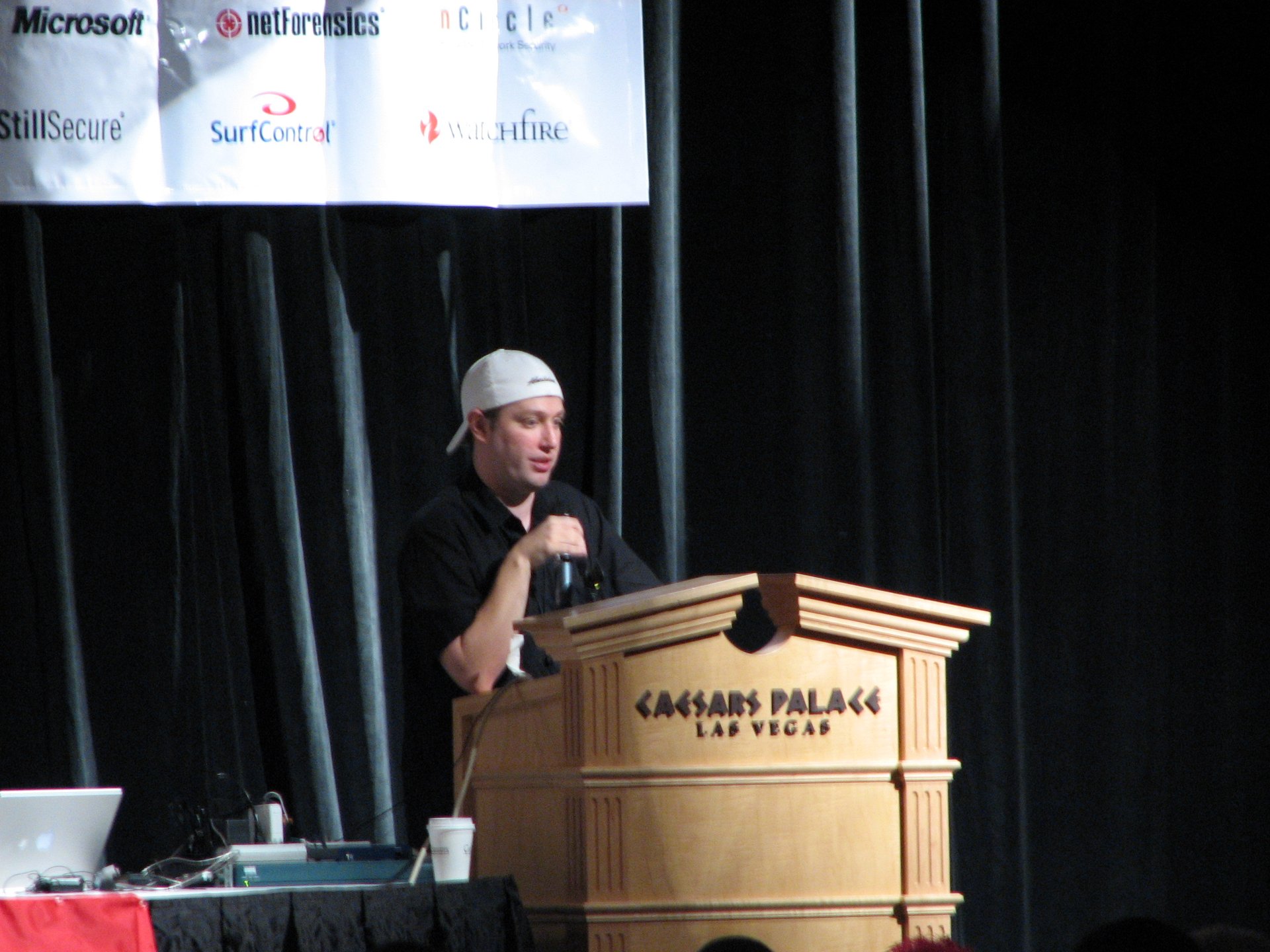
Security researcher Mike Flynn, at Black Hat USA 2005 in Las Vegas, Nevada, presents his findings on hacking Cisco routers.
Since those days, companies have developed formal, coordinated disclosure processes that give hackers a media embargo on their findings until the companies can “patch” the vulnerability in their code with a software update that includes the fix.
In some cases, companies also have “bug bounties,” cash rewards paid to hackers who present companies with a proof-of-concept for a zero-day exploit. Bounties can even feature limited-edition merchandise, like a T-shirt reading “I hacked the Dutch government” — if you find a way to hack the Dutch government and tell them first.
Weaponizing vulnerabilities for surveillance
More recently, however, zero-day exploits have become commoditized and weaponized — not disclosed to the affected company to make its software safer for users, but kept secret and sold to governments to spy on those users.
In addition to the growing list of governments investing in the ability to build tools for infecting devices with spyware, companies like Hacking Team or NSO Group hoard exploits to hack people, charging top dollar for access. The result of these instances has led to abuse of the technology by the governments of Mexico and the United Arab Emirates to spy on journalists.
Besides companies that discover and weaponize exploits in-house, brokers like Zerodium offer market prices for zero-day exploits designed to break into applications and devices that customers — mostly governments — can purchase for use in targeted surveillance. Compared to bug bounties and Pwn20wn prizes, gray markets like Zerodium’s have a clear economic edge in rewarding researchers with more cash for the vulnerabilities they discover.
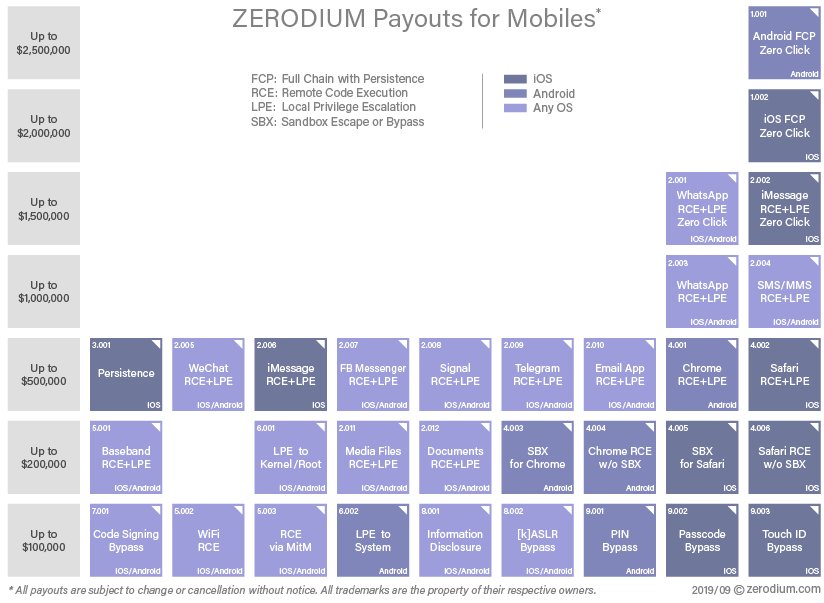
Image by Zerodium.
On the top shelf is the Holy Grail, a “zero-click” exploit that doesn’t require any action by the target to infect their device. Although this sounds super spooky, and it is, the average person is more likely to witness this kind of Hollywood hacking in a movie than in real life. As the $2 million to $2.5 million price tag suggests, it’s rare.
In addition to their scarcity, zero-day exploits lose the “zero” when someone discovers and reports the exploit to the company that makes the affected software. Once a copy of the exploit is obtained by a company’s security team (e.g., at Microsoft), that exploit is typically patched and then publicly disclosed.
Rendering exploits useless
This is a point of contention between exploit platform companies like Hacking Team and their clients. When a client fumbles an attack and the zero-day exploit ends up being discovered by the affected software companies, that exploit is no longer considered zero-day — the vulnerability is fixed and a software update is released to include the fix.
In a leaked exchange between Hacking Team and the Azerbaijan Ministry of Security, we can see that Hacking Team was less than excited at the possibility of a ham-fisted cyberattack leading to the target finding the exploit and reporting it to the company behind the software that it attacks, making it useless for Hacking Team’s other clients.
Once a zero-day exploit goes stale and becomes a known, patched vulnerability, it loses its economic value. So much so that even marketplaces hawking $15 exploits for unpatched WordPress plug-ins have been shuttered.
One reason for the bottoming out of those markets is that any customer interested in buying zero-day exploits already can read a vulnerability disclosure and build an exploit in a few hours with the publicly disclosed research someone else did when they discovered it — anyone who would use a zero-day exploit already has the ability to weaponize a known exploit.
The other reason is that if a target’s device is patched with the latest software updates, it’s immunized from the exploit and any attacks that leverage it. This is why applying any and all software updates on your devices is important — security-related software updates are vaccines for your browsers, smartphones, cars, and everything else that can be updated.
Being targeted with $2 million zero-day exploits is rare, but if it’s a concern for you, and you have a Mac or iPhone, consider enabling Apple’s Lockdown Mode, which is designed to “batten down the hatches” against advanced, state-sponsored spyware, like Pegasus.
Unfortunately, Android does not have an equivalent answer to this feature, but apps like iVerify can help you share logs — records of activity happening deep inside your device — with their security team to help look for clues that could hint at the presence of advanced malware.
It’s important to note though that these logs are generally not shared for a reason, as they can be very revealing about your device’s vulnerabilities and your on-device activities. This requires putting a lot of trust into a third-party security company to handle potentially very private data, which is generally not something we recommend, unless you have credible reason to believe you are in Predator’s sights.
Thankfully, most people are not the targets of sophisticated spyware, but definitely still targets of less advanced but still dangerous malware built on known software vulnerabilities. That is why it’s important to inoculate your devices, browsers, and other apps against known exploits by running your software updates, and don’t delay restarting when prompted to.
Security researchers who neutralize zero-day exploits, whether as their jobs at software companies, or through bug bounties or hacking contests, are turning down top-dollar gray-market prices to give everyone a means to better protect against the specter of cyberwarfare. As often as possible, make this important work count and maximize your device security by running your software updates.