Freedom of the Press Foundation recently released a report detailing a record number of arrests throughout 2020 based on comprehensive data gathered by the U.S. Press Freedom Tracker, a project in collaboration with the Committee to Protect Journalists.
Harlo Holmes, Olivia Martin, David Huerta, and Martin Shelton of our Digital Security Team weigh in on security threats facing journalists in the course of arrests, including the risk of device seizures, as well as law enforcement surveillance and data requests.
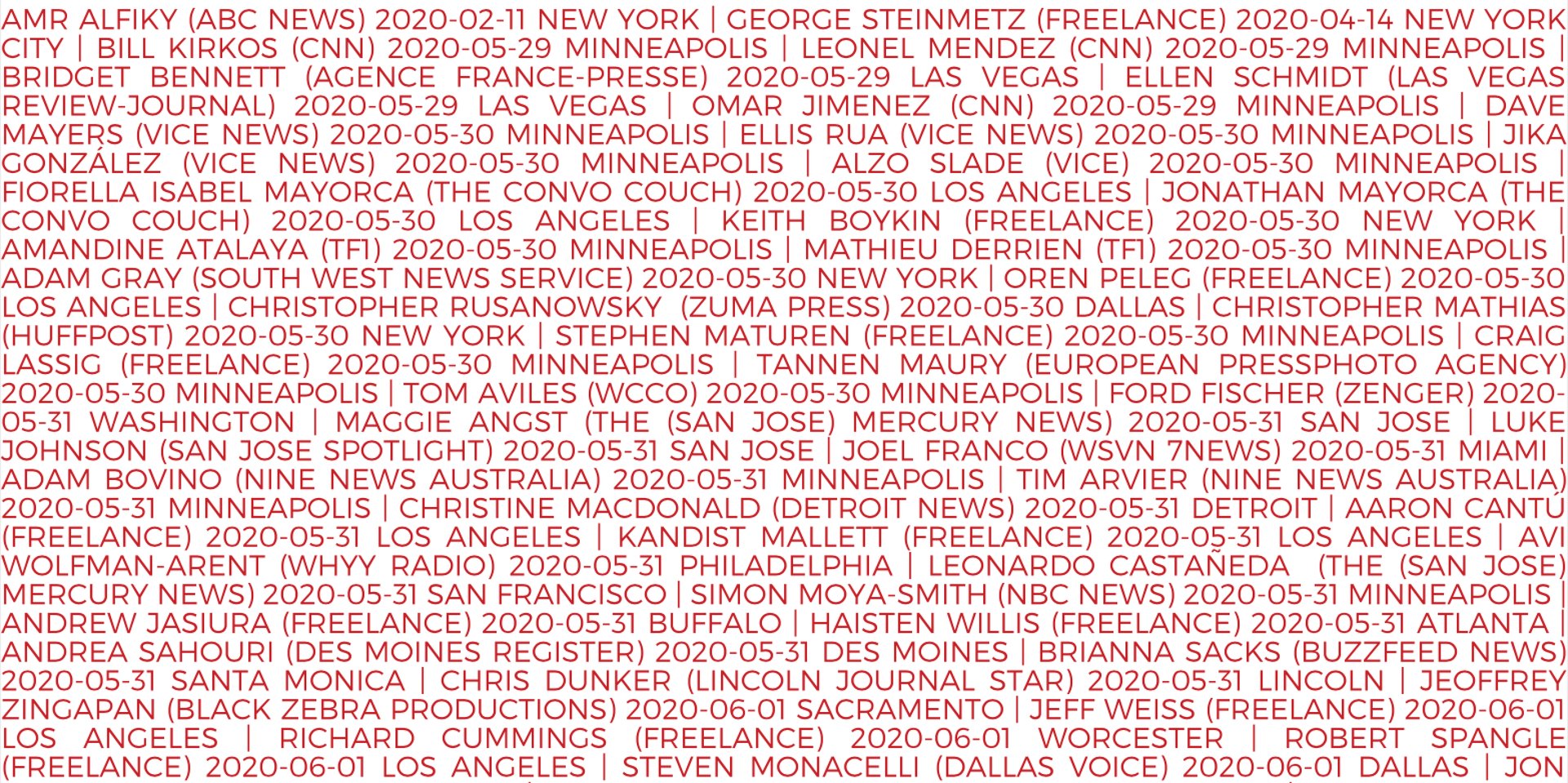
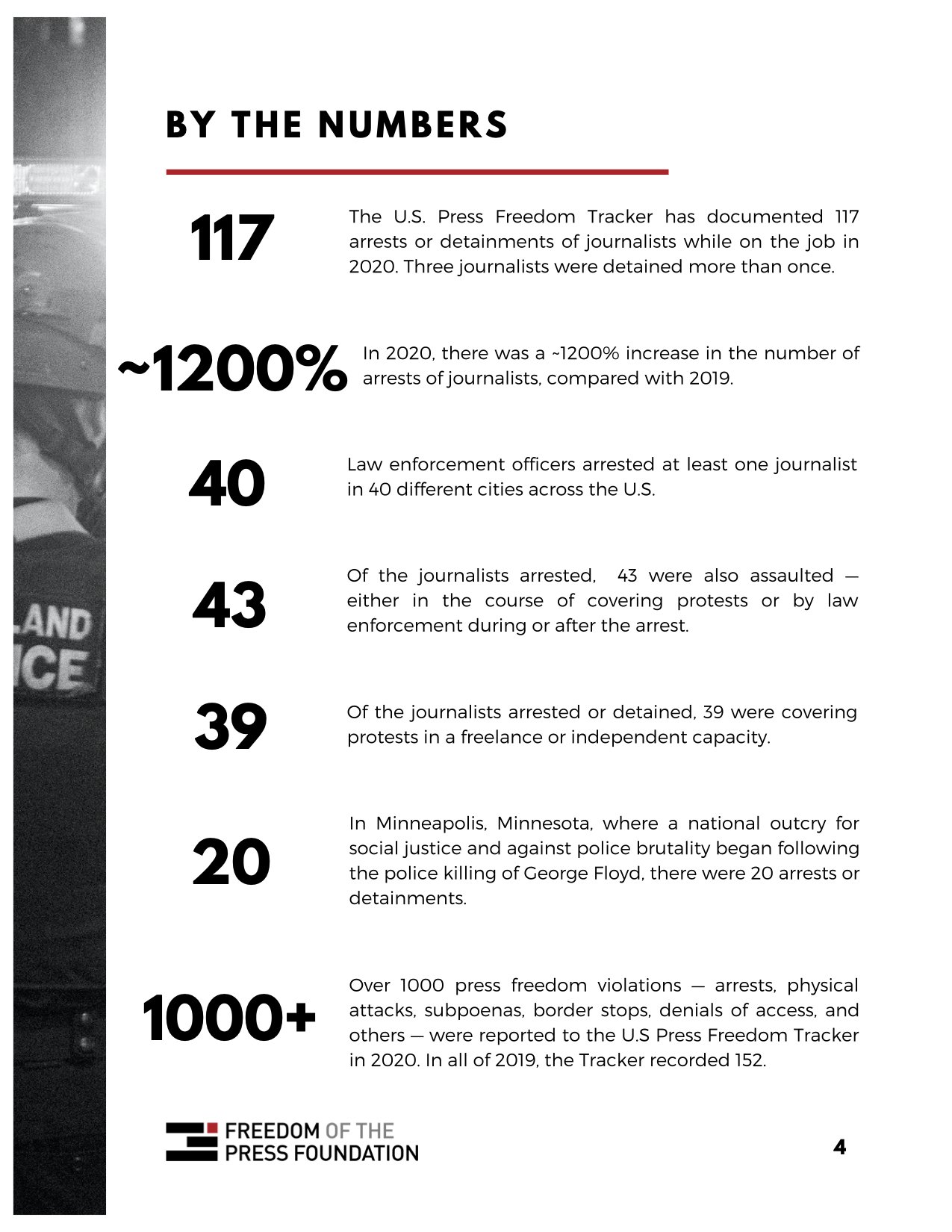
Olivia Martin: We see a breakdown of really important insights that have been gathered throughout the year regarding arrests of members of the press in the US. Something of note that I think has consequences for digital security is this: of the journalists arrested or detained, of at least 117 verified arrests, 39 were covering protests in a freelance or independent capacity. That's a very high percentage of the total number of arrestees identifying as freelancers.
Source: Freedom of the Press Foundation, in partnership with Committee to Protect Journalists: https://freedom.press/news/2020-report-journalists-arrested-us/
There are a lot of implications here, but it’s worth mentioning that freelancers lack a lot of the resources that journalists have at well-heeled news organizations. Not only do freelancers frequently lack legal resources, but also the resources to either undergo digital security training or have an in-house digital security specialist brief them on how to prepare to attend a protest. How to make sure that you're minimizing the sensitive data that you're bringing to a protest and that your devices are prepared. That if you're bringing a camera, how to take care to secure the footage that you take.
Harlo Holmes: Yes. I 100% am in agreement about that… As you mentioned, Olivia, being a journalist in the visual media rather than print media, if you're a photographer or a photojournalist or a documentarian, if you're behind the camera, there's no getting around being out there, and so the stakes are so high because you have to cover your face with a mask and you also risk getting tear-gassed, which I think puts them explicitly within the most vulnerable of the populations that we serve.
What I think is also interesting about that is it says 43 were assaulted either in covering protests or by law enforcement, during or after. What that means is that we are starting to see an uptick in journalists who have put themselves in the hands of either law enforcement or of people who just have this ridiculously fueled rabidity towards the press, which, living in this society where members of the press are actually attacked by other citizens for doing their job, is incredibly frightening, especially in a country that loves its constitution as much as it does.
Martin Shelton: So the report includes some details on specific reporters who were arrested, including freelancers like Christopher Rusanowsky. It sounded like he was detained and his camera equipment was seized.
We know that there's no encryption on memory cards in most professional cameras or, to my knowledge, any professional camera. I wonder if folks can talk a little bit about what are some of the risks inherent to having your devices seized, your equipment seized in the course of an arrest.
Harlo: Yes, and it definitely does depend on what was seized. On a typical camera, as you mentioned, there is no encryption on an SD card or a compact flash. A couple of years ago, we had a somewhat failed attempt to petition manufacturers to include encryption, but that was not particularly well-received. It's a very, very tough problem to crack, and so you can expect that someone will have their camera roll entirely gone through.
What's interesting about that is something that we also see afterwards, even if you don't have your camera seized, but not having encryption means that anyone who has access to that raw footage has the ability to use your photography, not as something that advances the story, but rather looks at it for its value as user-generated content. Meaning that a law enforcement agency could totally just take any particular picture from your camera roll in order to bring that as evidence into a trial.
While it's really hard to get people to think about the safety of footage as they take it in the field, getting people to think about the implications of why encryption still matters a lot, as far as editorial is concerned, is of huge importance. There is one really cool organization, the National Press Photographers Association. Their executive director — Akili Ramsess — is a badass who has all of these very seasoned tales about how she had to learn how to secure unsecured media when you're out in the field under circumstances like that.
Olivia: Think about a scenario in which a journalist who's covering a protest is arrested and has their camera confiscated. They're exposing whatever images they have on that storage media in their camera to the police. We can imagine a scenario in which this provides valuable information for police who might be able to go through those images and gather information to identify protesters that they're trying to identify in the course of whatever investigations they're undergoing. This could potentially result in an arrest. A protester being identified by the police.
Martin: Yes, it's definitely a risk. Thinking about the role as a press observer being co-opted into somebody else's needs.
This also reminds me of an incident of another reporter named in the report, Andrea Sahouri, who live streamed her arrest from the back of a police car. Olivia, you broke this down a bit. You want to talk about this case?
Olivia: Yes, sure. This journalist, I was shocked because I hadn't heard of this case before reading through the report, but we learn of this journalist live-streaming her arrest from the back of a police car. When I was considering how to talk about this case, I thought about the fact that this journalist has her phone on her, she's in the presence of police, she's using her phone to live stream. The purpose of live streaming for her is for the sake of accountability to share her story with her audience.
At the same time, I'm concerned as a digital security professional, about the fact that this person has their phone unlocked in the presence of police. When your phone is unlocked and you're in a scenario in which there's a high likelihood that your device could be confiscated, it can be really, really dangerous because if someone were to nab your phone as it's unlocked, they can see everything that's in your phone.
Now, that being said, I'm not sure there are a lot of different paths that that possibility could go down. An officer can seize this journalist's unlocked phone and see contacts, see messages that this journalist was sending, see footage and images that they took at the protest. I'm not sure how well this police force would be tasked to take copies of this data.
Harlo: Maybe this is a situation where we talk to journalists about preparing devices that are ready for the field in that way. I mean, you don't have to, but they say in the most extreme circumstances, streaming may be one of the best tools in your pocket in order to preserve yourself is to maintain visibility. This is why all of our advocacy around journalists who find themselves in trouble matters so much.
The act of live-streaming your arrest, that makes you undeniably visible — not only in terms of journalism but also just to protect yourself.
How do we do it safely? I don't necessarily know what Sahouri did herself, but one might want to think of preparing a separate device to go out into the field — one that has a limited number of contacts available, the people that you're going to be checking in with, the people that you necessarily need to meet with, people who might be able to represent you legally, et cetera.
It’d need to be able to connect to whatever social media platforms that are necessary in order to go live if you need to. Whether that means Twitter or Instagram, if you're comfortable with that going out, or Facebook Live.
Oh, God, whatever. Is Facebook Live still a thing? Or whatever the kids are using today, TikTok. I don’t know, wherever you need to go live.
If you don't need to stream live but you need to record, we do know that our phones are capable of taking photos and even recording video from its fully locked state. You don't actually have to unlock your phone in order to make that work. That said, your phone is still going to be unencrypted because it's on and that's how it works, but you don't necessarily expose yourself to more risk should your device be confiscated.
There's a little bit of a burden to bear financially speaking: "Oh, I have to get another phone, and I have to set it up this way in order to do this," but it may be something we're thinking about.
David Huerta: I worry how much photojournalists, in particular, would want to do that. I know some people that would be really into it because they were already doing pretty sensitive work. For a lot of people, having a second phone is already a big burden, but then knowing in advance everything you can possibly need, then put it into a different phone, when you already have everything ready on your main phone… It’s going to be a bit of a tough sell.
There are use cases for that. In the Before Times I was talking to someone at Shmoocon who worked at NBC, and he was talking about how you would prepare freshly re-installed wiped macOS computers that had access to everything they needed, their internal VPN, et cetera, so that journalists could cover things like the Kim Jong-un/Trump summit thing in Singapore, for example.
This is something that I think that a newsroom would have to do because I don't see too many individual photojournalists doing that. It's also just one of those things, right? As much as people want to give the advice that they shouldn't bring their phone to the protests —
Harlo: They do.
David: In all the protests that I have been to this year, phones are just out all the time. Except mine, I kept it off, but I’m an extreme edge case. It's one of those things where I think at this point it might make more sense to have more of a harm reduction approach where it'd be like, you're going to have your phone on you, this is how you minimize the stuff that's on it somehow. I don't know. I just know that people will bring their personal phones to an event.
Harlo: I love that you said harm reduction. I really, really do. I think that over the years that we've been working in this space, we've gone from taking this approach where you absolutely have to jump through all these ridiculous hoops, to the point where you've gotten to harm reduction is what matters. I think that that shows a lot of maturity within the space, and it's something that we do have to grapple with. If you're going to invest the time and money to get a second device in order to just go out on the street, fine, do that, but for the rest of us, at various times in our lives, harm reduction is worth investing our time.
Martin: A lot of these companies that focus on providing forensic services for police, they really want to find an unlocked device. That's the ideal scenario, but sometimes they don't find an unlocked device. What can they get?
Harlo: It depends on the phone. Certain phones are better protected than others against those out of the box tools that law enforcement use, but ultimately, if your phone is on, then everything is available. We also know from Team Upturn’s report that not only the digital security threat of, "We got your Samsung and we're going to brute force it open, defeat the lock screen on it," that's somewhat trivial for a lot of these devices that are out there that law enforcement agencies purchase.
It's not only that, it's like if you are arrested and your devices are seized, they make it incredibly difficult for you unless you just give up the passcode, and a lot of people do. They don't always have to go the route of defeating a lock screen because it's way more probable that you will just give up the passphrase, which goes against your rights, your Fifth Amendment rights (and depending on the scenario, your Fourth Amendment rights.) People do it anyways. That's why knowing legal recourse in order to protect yourself before you go out there is probably way more important advice than any of the digital stuff that we like to talk about. One group that offers this support is the Reporters Committee for Freedom of the Press.
David: I wonder how much we can advise on what to minimize in terms of stuffing your phone. There's things like disappearing messages that come in handy for this kind of situation, where even if the phone does get seized and then successfully copied into a forensic image, we still have a minimal amount of stuff to extract. Same thing applies to photos and contacts and apps that you happen to not need for the protest that you can just reinstall when you come back, like Facebook, for example.
I did wonder whether there are some steps there that could be useful. It also depends on, what are the cops looking for? Maybe there's a lot of text messages that don't need to be there. I don't know the app data they're looking for, but I can imagine some common suspects — Facebook, chat apps in general. We can look at those apps and be like, maybe you don't need to have this or that installed.
Harlo: That comes back to our discussion about whether you should get a second device or are you going to bring your phone? From the resources perspective, I personally would rather pay 100 bucks to get a second device that I can safely bring out, than to spend the hours it takes to delete and reinstall Facebook, to agonize over every single text message that I've ever received and wonder if I should delete it before going outside of my door. I would rather actually just get a secondary device.
I've been in that situation where I had been paralyzed with fear, looking through every text message that somebody had sent me and being like, "Should I delete this? Should I delete this? Should I delete this? Is the security at the border going to think twice about this particular exchange?" I'd rather not do that.
David: I can think of few/no photojournalists who are going to find another phone, because it is a low-pay high-cost situation, but that being said, there's other risks besides cell phone tracking at these things too.
Harlo: It depends as we say. I want to get a mom tattoo with the heart and whatever and it just says "it depends." Oh, my gosh, we should do that.
Olivia: Oh, that's good. That's so good.
Harlo: Let's do it.
Olivia: It's a team bonding exercise.
Martin: It's going to have our new Digital Security Team logo and Harlo's face and her crossing her arms, and it says underneath "it depends."
Olivia: I dig it.
Martin: Another thing that was in the report that I thought was really interesting… The Department of Homeland Security tapped protesters' phones and it established intelligence reports "on journalists who published leaked documents about the agency's operations." There's a little writeup in the Washington Post…
A senior Department of Homeland Security official told a Senate committee earlier this month [July] that the department had not collected, exploited or analyzed information from the electronic devices or accounts of protesters in Portland, Ore.
But an internal DHS document obtained by The Washington Post shows the department did have access to protesters’ electronic messages and that their conversations were written up in an “intelligence report” that was disseminated to federal law enforcement agencies, including the FBI, as well as state and local governments.
I was curious. When we're talking about tapping phones, what could that potentially mean for protesters? Then also thinking through what kinds of things you would expect to see in one of these intelligence documents?
Harlo: It's insane that intelligence reports are being collected around journalists. I can't think of anything more absurd, anything more un-American — at least by our ideals, not necessarily by our behavior, because it's happened before. It is just a travesty. We can talk about the mechanics of how this phone tapping is happening and the meat and potatoes of what these intelligence reports contain.
Olivia: Yes. It looks like these DHS intelligence reports involved two different journalists. One is a reporter from the New York Times and the other one is the editor in chief of the blog Lawfare. The purpose of these intelligence reports appears to be to announce to members of DHS that these journalists had published leaked unclassified documents about DHS operations in Portland.
They also included written descriptions and images of the tweets, and, this is directly from the piece: "Written descriptions and images of the tweets and the number of times they had been liked or retweeted by others." That raw data.
While this is very unnerving, it appears as though shortly after this practice started, the Acting Secretary Chad Wolf called upon the rest of the agency to immediately discontinue this practice.
Harlo: What I think is really interesting about this is that… y'all remember just how you felt in the weeks and months after the Snowden revelations dropped and when we learned about mass surveillance and the reason why they would do it. It's because if you're three hops away from a "suspected terrorist," then your call records can be totally scooped up, no problem, and then realizing that if you did the math, that actually meant practically everyone.
Then, over the years, since the Snowden revelations, one of the things that was so great about it, the outcome, was that Congress reined in the surveillance capabilities that allowed gathering phone records in the ways that they did. What we're learning from these is that nothing has changed and that you seal off one particular avenue to allow people to surveil everybody, but then they just find another way.
Ed did say, and part of his rationale in doing what he did, was like, "Guess where this is heading next, folks? You say that it's about the outside, about other countries? It's not. It's about you. It's about you as an American." You are seeing that and we've let them get away with it.
Martin: One of the things Edward Snowden revealed was a secret interpretation of Section 215 of the Patriot Act concerning the telephony metadata surveillance program. Like you said, that's been reined in somewhat, where now, the intelligence community needs to go to telephone companies in order to make requests under that particular authority, but there are multiple overlapping authorities.
Another thing that he pointed out was, inevitably, that includes Americans' metadata, even if it's scooped up "incidentally." If the authority was there one way or another, the technical capability was there one way or another. What we're seeing is that that was a foreign intelligence capability also scooped up Americans. The intelligence reports mentioned in the Washington Post targeted U.S. reporters and civilians in a more deliberate way, who were speaking over social media.
Olivia: Yes. Also in this Washington Post piece that we're discussing, it not only tells us that DHS established intelligence reports on journalists, we also learn that DHS "tapped protestors' phones." Looking deeper into this piece, I see it's not entirely clear how the DHS got access to protestors' communications. We do know that the intelligence reports that DHS was circulating included messages between protestors on an app called Telegram.
These are messages that came over a group chat on Telegram, where they're just discussing tactics for organizing and localizing protestors on the ground in Portland. What's not clear here is exactly how they gained access to this particular group. There could be a couple of methods that they could get access to these messages. One could be that they have an informant within the group.
Harlo: I think that's the most likely.
Olivia: Yes. We do know that Telegram itself does give users the option to start a group, either with end-to-end encryption applied or with no end-to-end encryption and just transit encryption applied. This is like a meta-discussion about digital security and about proper usage of messaging apps for sensitive conversations. We do always advise that if you're using a chat app for sensitive conversations that, at the very least, you make sure that it supports end-to-end encryption, so as your messages travel between your phone and the people that you're speaking to, it's not accessible to anyone else who's snooping on the line, or the app provider itself.
Harlo: That is always 100% evergreen advice. End-to-end encryption is, as they like to say, facts on the ground.
That said, it can only go so far. As far as Telegram is concerned, yes, there's always the problem, the same thing with Discord, it functions the same way, that because group messages are not end-to-end encrypted and only encrypted to and from the service, then you do run a risk of any person reading that, but I don't think that that's the problem.
I think that the encryption with apps like Telegram and Discord, the regular encryption, not the end-to-end mess or whatever, is robust enough that I'm not expecting the Department of Justice to be literally hacking into Discord or into Telegram in order to get into your chats. They have an informant in the chat. That's how that works. Back in every single case that we've seen about a group being popped, whether that's coming from Telegram or from the WhatsApp chats in the Governor of Puerto Rican’s cabinet, whatever. All of that came from the fact that no matter what encryption you're using, you have a mole in your chat. Don't worry about it.
These anecdotes show us the danger in these types of insecure communication workflows, where people are encouraged to speak very, very freely, very willy nilly in ways that will get them ensnared later on if the chat’s supposed to be used in a professional capacity. While, once again, we've got that evergreen advice about using end-to-end encryption, cryptography implements trust, mimicking the ways that humans implement trust, but you can't not have both, especially when you're organizing.
David: As much as I agree with all that, I do want to take the opportunity to dunk on Telegram's garbage encryption, though.
Harlo: Yes. Preach. Preach, David.
Martin: Never miss a chance.
David: It's so bad. It's late 90's MTProto. It's like, what is this? Should I get my Swatch Internet Time watch to use this? Should I get my inflatable transparent couch and start playing Crash Bandicoot on the PS1? No, y'all, we have modern encryption standards now. The Grugq and 248 Stack Overflow users agree.
Harlo: Oh, my God, encrypt Crash Bandicoot, though, please. Yes.
As we're talking about Telegram, one of the reasons why I'm pretty sure it had to be like a mole in the chat is because for better or for worse, dunk on that encryption all we want, but Telegram does not play well with law enforcement requests for people's conversations.
First and foremost, there's a time-sensitive aspect to it. It would have taken months and months for them to read chats that were happening in real-time if they went through legal channels via Telegram. There’s also some precedent, for instance, how Telegram reacted to a request from the Chinese government during the very beginning, the first revolutions in Hong Kong, that they weren't going to play those games.
Yes, I wouldn't touch Telegram with a 10-foot pole for my chats, but I do respect them from that perspective where they're just like, "We're not going to give up our data. We're not going to respond to these requests."
Martin: I also wanted to ask a little bit about some of these charges still pending. At the time of publication the arrest report said 16 journalists are still facing long-term legal struggles. They might be summoned, and this is obviously an extremely stressful situation where you don't really choose when you're going to be there. I wonder if we could talk a little bit about some of the ways in which this could intersect with data requests and how this is likely to affect the journalists and their ability to report on not only these events but do their work more broadly.
Olivia: What do we know based off the precedent? The example that comes to mind here in recent history is the case of the nine professional journalists arrested back in 2017 during the J20 protests against the inauguration of President Trump.
While covering these protests, nine journalists were arrested, and they were arrested on felony writing charges along with over 100 other protestors, medics, and other observers. What we saw was that it would take almost a year and a half until the last felony charge was dropped against one of these journalists. This meant that for some of the journalists who were arrested, these charges weren't dropped in a short amount of time, and instead, they had to take on incredible legal costs.
There's also time involved in keeping up with your case, court attendance, all these things. We know that this happened three years ago, and so looking into what's plausible, this could be a long road for these journalists. Thankfully, all the charges were dropped against the journalists covering the J20 protest, and we hope the same for these journalists who are still facing charges.
Martin: This is extremely stressful. On top of that, there’s not only data that could be pulled into court from seized devices, but your newsroom might have access to multiple channels for backing up data or saving it to the cloud.
A lot of newsrooms use cloud-based services for storing their data. You don't necessarily want to depend on just the device that's in your hand or in your bag in order to make sure that you have the reporting that you need.
As a consequence, sometimes we’ll remind folks about some of the ways that service providers are not only vulnerable to legal requests, but might actually have an administrative process in place so that they can easily turn over data in case they receive a law enforcement request. eDiscovery tools typically allow essentially anything that can be administratively accessed to be recovered from a cloud service.
Say that you're saving your documents or uploading videos to Microsoft 365 or Google Workspace, or even other tools, or other cloud providers. These tools make it very easy to search through organizational data and do what's called a legal hold, where specified data is preserved within an account. Even if you delete something, it's not deleted. You might be compelled to turn that over as an organization or any of your work product or process documentation. The administrator, and whoever they give access to, has a lot of control. Law enforcement data requests could also go directly to the service provider, making an end-run around the subscriber organization.

