If you have journalist friends like I do, you know that most of them don’t get into this line of work for the overwhelming paycheck. That means they don’t always treat themselves to gadgets and services that will make their jobs safer and easier. So maybe you can treat them instead.
For instance, many journalists are missing important tools that could help them do their job more safely. Plenty of gadgets (e.g., computer hardware) can help protect journalists' security and privacy. And a few subscription-based services can help protect journalists, too, as they work on the web.
Explore the journalist gift-giving guide below to see some of our recommended gadgets and services for the journalist in your life.
Gadgets
Security keys
When anyone, whether you or your journalist, log into a website, access to their account typically only requires a password. However, a growing number of websites allow them to better secure their account with a second piece of information — a second “factor” — beyond their password. We sometimes call this two-factor authentication.
A security key, such as a YubiKey, is a small device that they can use as that second credential beyond the password that’s required when logging in. When prompted during login, they just tap the button on the security key. That’s it.
There are many kinds of security keys, with many form factors. The cheapest and simplest one we recommend is the Yubico Security Key ($25), which supports the USB connection they’d find in any old-fashioned USB port, as well as a wireless NFC connection on mobile devices. Yubico also supports other connection types (e.g., the standard iPhone connector), but it’ll cost extra.
Note: Many new devices (e.g., MacBooks from 2016 and beyond) may need a USB Type-C YubiKey or a Type-C adapter. Here’s a list of Type-C adapters confirmed to work with YubiKeys.
Learn more about two-factor authentication here.
- Security keys may be purchased from Yubico, starting at $25.
- Another option: USB Type-C adapters.
Webcam stickers
Get that journalist a webcam sticker. Journalists love webcam stickers.
If their device is hijacked by malware, a hacker may have all of the same permissions as they do. The journalist owns it, but so does the hacker.
Enter some of our most unhackable anti-surveillance technology: Stickers.
If someone breaks into the journalist’s device, a webcam may be the least of their problems. But it’s nice for them to have the peace of mind to know they’re not visible on their webcam unless they choose to be.
Check out the store for Freedom of the Press Foundation (FPF) for webcam stickers, which can be reapplied and last months at a time.
- FPF offers webcam stickers for $10.
- While you’re there, shopping for your journalist, check out the rest of the store.
Backup hard drives
Computers inevitably break down and are sometimes lost, stolen, or even remotely hijacked. Having a personal data backup can save a lot of heartache.
Unfortunately, we see a growing number of organizations and individuals hit with ransomware attacks designed to crawl through a network and encrypt its connected computers, rendering them useless. Those computers can only be unscrambled under one condition: Pay the attackers a decryption fee.
This is exactly what happened to a San Francisco Bay Area public radio station in 2017. Even more commonly, devices are simply lost or stolen. This is why it’s wise to make a backup to an external hard drive, which your journalist can use to roll back to a previous snapshot of their activity on their devices.
Windows users can back up and restore devices using File History, while Mac users can make backups with Time Machine. External hard drives can also be configured to encrypt only specific files or to archive sensitive data for long-term storage. (Check out our guide to learn how.)
- Wirecutter: Pick whichever is cheapest and does the job. (Note: While a 2-4 terabyte drive will be plenty of space for most reporters, filmmakers will eat up hard drives with digital video, and will appreciate more space.)
Chromebooks
Hear me out: Chromebooks have a lot of use cases that make them great for security. First, a Chromebook is different from a normal laptop because it’s intended to be a portal into online services, as opposed to a device for working on local documents, so the user doesn’t really need to store any data on the device. This can be beneficial when traveling to sensitive locations, or if the journalist in your life is concerned about the device being seized.
Because most malware will be designed for other operating systems, it’s also a relatively safe environment for launching risky files and wiping dodgy USB devices. And because the stakes of wiping a Chromebook are quite low, users can easily power wash (basically factory reset) their device to scrub any unwanted data and start anew at any time for extra assurance that the device is secure. Just aim for a new-ish Chromebook to ensure it receives 10 years(!) of security updates.
- Wirecutter: Pick whichever is in your budget range and is “good enough.” Note that space on a Chromebook matters somewhat less than a normal laptop, because most data is backed up to the cloud.
Online safety reading
The journalist in your life probably wants to cozy up with a security book, right? Right.
We have a tough time finding books with strong and accessible security advice for beginners, but there are a few out there. While unpacking the many risks to personal information and our own well-being online, “Keep Calm and Log On” does an exceptional job of framing issues of media literacy in an empowering way. In 2021, scholar Susan E. McGregor published “Information Security Essentials,” a textbook based on extensive scholarship and experience examining digital security for newsrooms. This will be an invaluable resource to journalists for years to come. Finally, to learn about the visibility of our information online, we also suggest “How the Internet Really Works,” by Article 19. With clear explanations accompanied by friendly illustrations, we can imagine this being a useful gift to both journalists and their kids.
- "Keep Calm and Log On" by Gus Andrews, $24.95 (price may vary).
- "Information Security Essentials: A Guide for Reporters, Editors, and Newsroom Leaders" by Susan E. McGregor, $29.99 (price may vary).
- "How the Internet Really Works" by Article 19, $19.95 (price may vary).
Subscriptions
Password managers
People have a bad habit of reusing passwords, and hackers know this. Every week, it seems like there’s a story about a large-scale password breach; this is why it’s so important not to re-use the same password. At the same time, using unique passwords on every account is impractical — unless your journalist has a password manager.
A password manager simplifies the process of generating and using dozens of strong, unique passwords through a dedicated password “vault,” which can only be unlocked with one password, using authorized devices. Password managers (e.g., 1Password) will allow users to automatically fill out all of their passwords on their devices.
Saving time and securing accounts are both significant advantages for reporters with password management subscriptions.
- 1Password gift cards. (Note: In some cases, journalists can get access to some free services through the 1Password for Journalism program.)
- Learn more about password managers.
Virtual private networks
When connecting to websites, those websites and intermediaries (e.g., an internet service provider such as Comcast) can see the traffic and information about where the user is connecting from, such as their IP address. This is generally not great for reporters, particularly when conducting investigations.
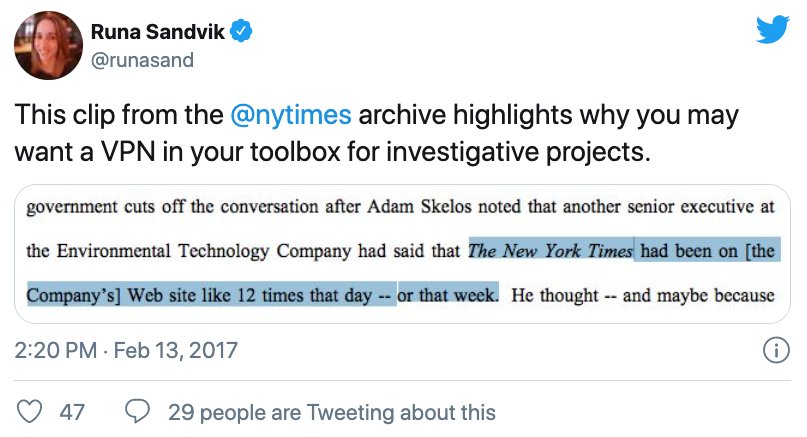
Credit: Screenshot via X.
Enter virtual private networks. VPNs can help obscure the user's location to websites and their traffic to their own internet service provider.
So how does this work? VPNs encrypt and tunnel web traffic through a remote location, obscuring the user's actual location. When using a VPN, anything a network intermediary gathers is encrypted and illegible to them. However, the websites your journalist visits can still unscramble the traffic as normal — only the user's apparent location has changed. Free VPNs are not worthwhile, because they have a track record of logging personal data and compromising privacy.
- One of our recommended VPNs is Mullvad, which costs €5 per month. Note that there are many competitive options, but with Mullvad, you can purchase access codes and give them away freely to your favorite journalist.
- Read our in-depth guide to VPNs to investigate more.
Data privacy services
Many reporters — particularly those focused on politically sensitive work — are the targets of coordinated digital attacks that aim to hijack their online accounts. Sometimes these attacks also target physical locations, such as their homes, or their families. Much of their personally identifiable information is available through search engines, public records websites, genealogy websites, or “people search” sites (e.g., Spokeo.com), which may aggregate all of the above. While many of these websites have “opt out” pages, because there are so many, and so many will repost user data every few months, it becomes a nearly full-time job to opt out from such services.
Removing someone’s personal data from the web is an uphill battle, but data privacy services can make this kind of attack harder. Services like Optery or DeleteMe will remove your journalist’s data from dozens of websites for a year at a time, for one or more people.
- Sit down with your favorite journalist and pay for the first year of their subscription, or if appropriate, add them to a family plan.
- Check out DeleteMe pricing tiers and Optery pricing tiers.
Learn more about how reporters can prepare for, and respond to harassment.