In September 2019, Eric Trump tweeted a screenshot of an email that circulated through the Trump Organization from Washington Post reporter David Fahrenthold. The president’s son called out Fahrenthold’s “tactic” of offering to talk and receive documents anonymously.
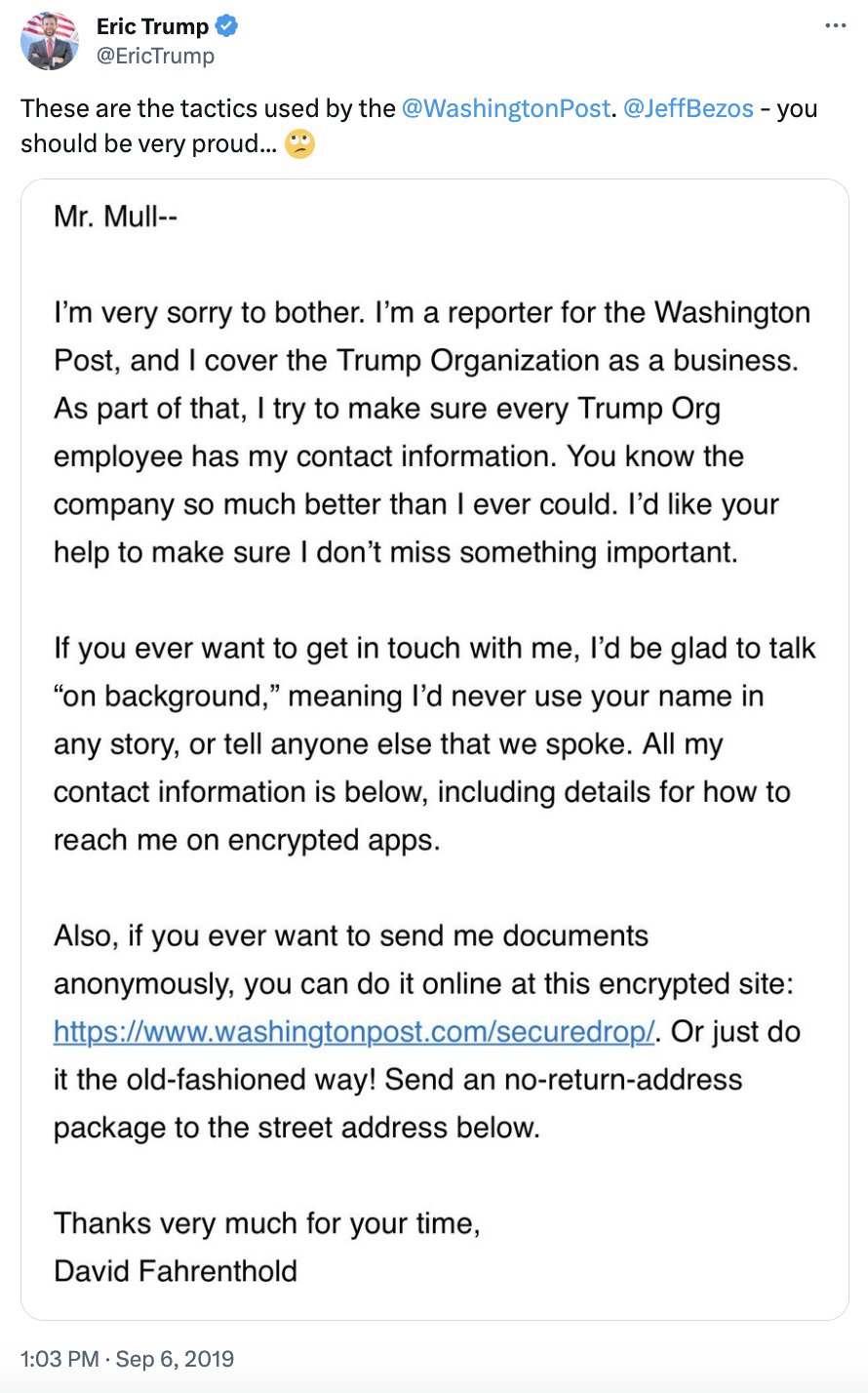
Despite this insinuation, there’s nothing scandalous about the long-established practice of letting potential sources know you’re ready for their scoops — unless what your source does in response gets them outed. Here are a few scenarios of what could get them in trouble:
Scenario 1: They hit the reply button
“The ‘e’ in ‘email’ stands for ‘evidence’” - Cybersecurity proverb
One of the biggest risks in contacting sources via email is the instinct to reply. The source could respond by asking how to use the “encrypted apps” Fahrenthold mentions or, without knowing the importance of encryption, start spilling the tea right in the email thread.
By the time you get back in contact to suggest a more secure channel, they’re fired.
What happened?
Email isn’t just accessible on the computer you view it from. It’s also visible to computers that belong to the email provider — in other words, the email server.
When a potential source emails you from their work address, they’re probably emailing you and their employer, whether they intend to or not.
Although there’s some variation between the technology protocols being used behind the scenes to store and transfer email between servers, we should assume that any message a would-be source receives, sends, deletes, or drafts can be viewed by their employer. In fact, services like Google Vault, a feature available to companies using Google’s G Suite, let employers see every revision made to a message in their drafts.
Scenario 2: They use an encrypted messenger app ... on their employer’s Wi-Fi network
When we connect to workplace Wi-Fi, we’re typically giving the network administrator tremendous power to monitor our online activity. Encrypted messaging apps are still noticeable to network administrators, even if they can’t read the messages being sent.
Signal is a fantastic resource for truly confidential conversations between journalists and their sources. Unlike email, Signal messages are “end-to-end encrypted,” meaning no one beyond the sender and recipient can read the messages — not even the owners of Signal.
Although messages and other metadata are protected from eavesdropping by Signal’s owners, its usage may be detectable by the operator of the network you’re connected to.
On a smartphone, this can be a cell or Wi-Fi network. If a source is using Wi-Fi operated by their employer, that employer can see some degree of your online activity. Even encrypted activity may reveal clues about what you could be up to; although Signal is popular among security enthusiasts and many journalists, it’s far less popular than other messenger apps and may stick out to a network administrator in a sea of otherwise normal-looking online activity.
In 2013, an anonymous bomb hoax by a Harvard student was thwarted by the FBI, not because they could see that the threat came from him, but because he was the only person using the Tor anonymity network on Harvard’s Wi-Fi when the threat was made. Tor is encrypted, giving the user a secure connection to the web. But even if a network administrator can’t tell what a Tor user is doing, the usage of Tor itself is (usually) detectable. The student’s connection to the Tor network was suspicious enough to narrow down the list of potential suspects to one person on the Harvard network.
If Tor becomes more popular, its common usage will make it less suspicious. Same thing goes for Signal. Normalizing tools like Tor and Signal can give potential whistleblowers a kind of herd immunity from being singled out for using them, even just for bland chats and searches.
Speaking of Tor ...
Scenario 3: They use SecureDrop, but from their work computer.
Much to the delight of many of my colleagues, Fahrenthold suggests using SecureDrop, a whistleblowing platform developed right here at Freedom of the Press Foundation (FPF). SecureDrop is designed to go beyond confidentiality and provide a way to communicate with sources whose anonymity is enforced by its design, rather than by a mere promise.
SecureDrop sites (such as the one The Washington Post operates) rely on the Tor network for anonymity. We recommend using it through the Tor Browser, a web browser similar to Firefox, designed to only operate within the Tor network.
Aside from the aforementioned detectability of anonymous Tor usage on an employer’s network, the Tor Browser itself may look suspicious if found on a work computer. Many employers use remote PC access software, allowing them to see everything a source can see on their work computer’s screen. That includes conversations with you or a visit to a tips page.
Consider asking your sources not to reach out to you from work
Ultimately, the panopticon of the modern workspace and work-provisioned computers and smartphones leave little room for whistleblowing on the clock.
That’s why SecureDrop landing pages, for example, generally include a recommendation for use on a public Wi-Fi network, rather than a work or home computer that can potentially be traced back to you. It’s important to tell potential sources this too.
Cold-emailing workers at a company you’re investigating is a time-honored tradition, one which should be updated to consider the dangers of modern workplace surveillance described above and to let sources know how to reach out without getting fired.
If your news organization doesn’t have a SecureDrop instance, check out our guide on how to get started, or reach out to us to learn about more options for secure tip lines and source protection.