What does antivirus software do?
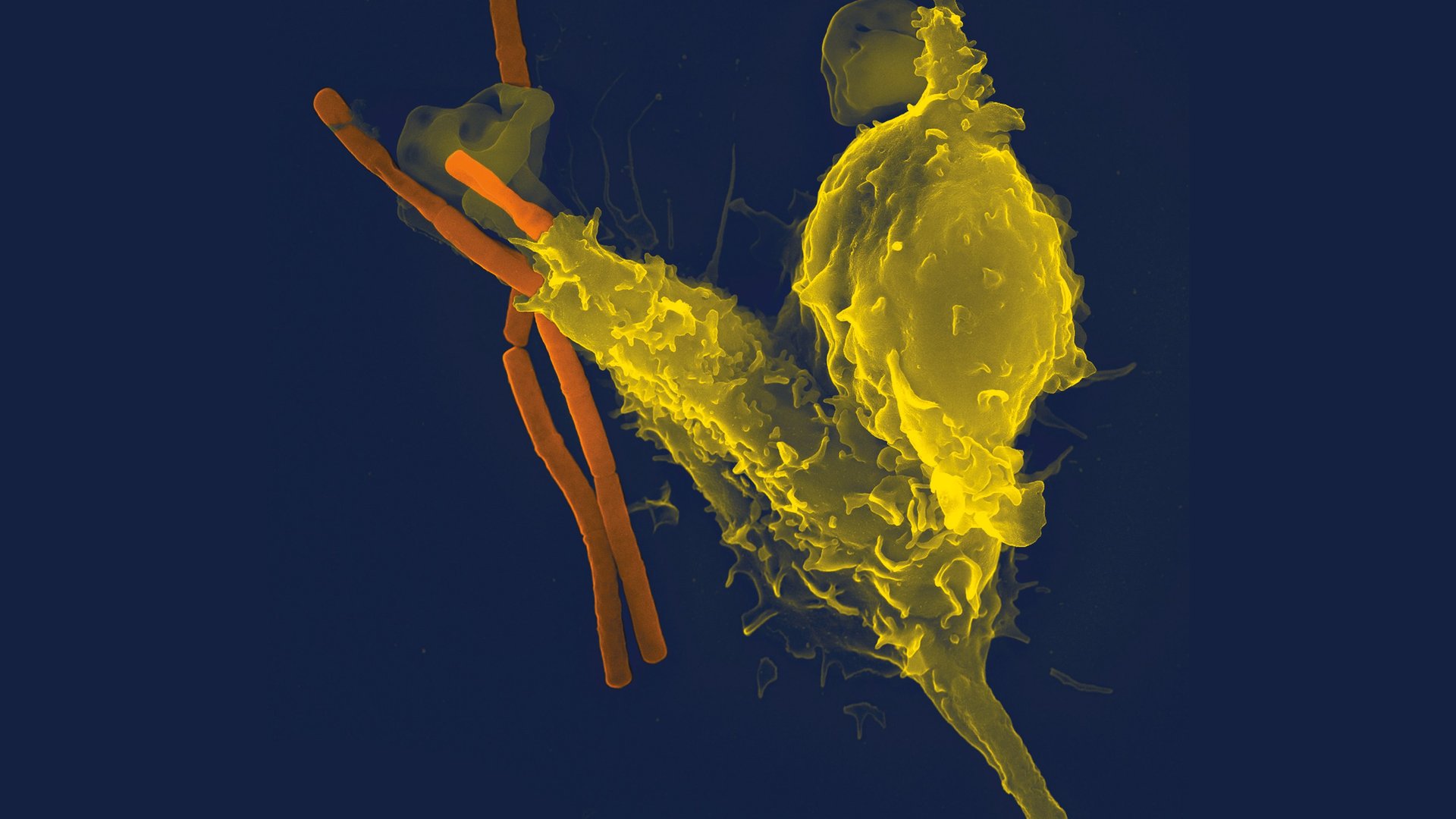
Antivirus software is one of the oldest products to come out of what is now an entire industry around cybersecurity. Each product has its own set of differentiating features, but a common aspect to all of them is being able to find and nullify malware (viruses, worms, etc.). Much like a biological immune system with antibodies that detect pathogens, antivirus software can detect known malware by using a collection of malware definitions, or "signatures," weighed with other signifiers based on the malware’s behavior or composition. For example, does a suspect program contain code seen in other malware? Is it communicating with servers known to be used for cybercrime? The combined heuristics are then used to detect and remove or quarantine the malware, to prevent it from changing anything on your computer.
These signatures come from the antivirus industry, along with others in adjacent industries and academia, investing research time to stay abreast of emerging malware designs. They won’t know everything however, and bespoke malware designed to infect only very few and specific targets may fly under their radar. These strains are rare, however.
Sometimes malware takes the form of simple, unsophisticated viruses that their creators use to trick users into letting them hijack their computer for use in automated attacks. For example, an attacker may use malware to take over a target computer and add it to a botnet, a collection of hijacked computers they control, allowing them to leverage the combined forces of several hijacked computers to carry out cyberattacks and other cybercrimes. Other times, malware is even more sophisticated. Kim Zetter's 2014 book “Countdown to Zero Day,” chronicles one of the better-known examples: the then-mysterious malware we’ve come to know as "Stuxnet," which was analyzed by antivirus industry researchers across different companies.
However, some antivirus companies have come under fire for their role in what could be described as antivirus software doing what it's designed to do. Like many other antivirus products, some offerings from cybersecurity company Kaspersky use a form of cloud-based machine learning to detect malware beyond simply checking signatures and statistical heuristics. In theory, this could mean that someone creating new, not-yet-discovered-by-researchers malware on their computer could have it detected without a pre-existing signature.
In the case of a malware author affiliated with the Equation Group — a hacking group widely believed to be affiliated with the NSA — new malware was found by the Kaspersky antivirus software installed on the author’s computer. Reportedly, this user had the Kaspersky Security Network feature enabled, which automatically uploads the broad set of potentially malicious files, in this case including documents full of sensitive NSA files, to Kaspersky’s servers. It's difficult to prove whether targeted exfiltration was involved and impossible to verify that Kaspersky deleted the files in question, as they claimed to. Currently, the U.S. government forbids the use of Kaspersky software on its computers.
However, the reality is that all antivirus software requires a high level of trust due to the deep level of file access it needs to work. Antivirus software typically needs access to inspect every single file on your computer, which brings up the privacy concerns one would have for any software with that level of access, such as, for example, the anti-virus company selling your browsing data. This is why it’s important to review the abilities and terms of service of the features you’re opting to use. If that antivirus software has access to files on your computer from their servers, it may be worth finding one that doesn't. If you’re making the next Stuxnet for a three-letter agency, don’t use antivirus software that’s smarter than you are.
Even if you’re not creating cyberweapons, however, journalism does entail the protection of sensitive documents and the sources those documents come from. With what seems to be a political crossfire between antivirus and intelligence agencies, there may be risks to your source to consider if they happen to be blowing the whistle on one side or the other.
What does antivirus software not do?
Speaking of malware powered by stolen exploit code from the Equation Group, ransomware, a type of malware which locks up your computer’s files and demands you pay a ransom to unlock them, has spread around the world since 2017, slamming global logistics companies into a full stop and sending affected newsrooms back to the stone age. A common aspect of many of these stories has been that they were behind on their version of Windows or its software updates. In some cases, affected systems were also using a really old version of Windows that was no longer receiving software updates at all. Windows XP and Windows 7, for example, are well past their expiration date. Windows updates available to newer versions of Windows include fixes to vulnerabilities discovered by security researchers, including those working at antivirus companies and beyond. If those updates are not downloaded and installed, those computers won't contain those fixes, or “patches,” and remain vulnerable to the kind of malware that takes advantage of those vulnerabilities, as the more dangerous strains of ransomware generally have.
Microsoft’s security advisory from May 2017 sums up the situation nicely:
This vulnerability was fixed in security bulletin MS17-010, which was released on March 14, 2017. We remind all customers to keep computers up-to-date.
The exploit code used by this threat to spread to other computers was designed to work only against unpatched Windows 7 and Windows Server 2008 (or earlier OS) systems. The exploit does not affect Windows 10 PCs.
Antivirus software, like antibiotics, may help inoculate against known malware (assuming your antivirus software detects it), but ultimately, the system-level patches that are delivered by your operating system’s software updates are what give it innate immunity. In addition to Windows, this is also true for Macs as well as iOS and Android smartphones and tablets.
Do you have a few minutes, maybe a lunch break or a long meeting with your editor coming up? Take a moment to update your operating system now (and lock your computer before walking away from it):
Windows 8.1 users: Start menu > Control panel > System and Security > Windows Update
Windows 10 users: Start menu > Settings > Update & Security > Windows Update
Windows 11 users: Start menu > All apps > Settings > Windows Update
ChromeOS users: Settings > About Chrome OS > Check for updates
Mac users (Catalina or newer): Apple menu > System Preferences > Software Update
iPhone and iPad users: Settings > General > Software Update
Android users: Some Android device manufacturers may also be significantly slower than others in providing security updates — if they do at all. AndroidOne-certified devices generally have a quicker update schedule than others though. Where to check for updates varies by vendor, version, and carrier — for example, many Samsung Android users will need to navigate to Settings > System updates while users of some AndroidOne-certified devices would navigate to Settings > System > Advanced > System update. Refer to your device manufacturer's website to learn where to find your device's update settings.
Going back to the deep level of trust required for antivirus to work, there’s an outsized risk involved if your antivirus software itself is found vulnerable, since that deep access could give security breaches deep reach. That’s why it’s also important to keep antivirus software up to date along with your system updates in order to address any published security issues that might need to be patched up.
Taking these simple steps as quickly as you can and, better yet, setting your system updates to happen automatically, will dramatically reduce the chance of malware infecting your devices.
Do you need antivirus software at all?
Since software updates patch the holes in our systems malware is designed to exploit, do we really need antivirus? It depends. The utility of having antivirus is that it knows when something installed on your device is malware even if we don't. We may be tricked into installing software we feel is perfectly legitimate, but may turn out to have a hidden purpose. As very careful individuals who look at every email attachment and link with suspicion, we might be okay without antivirus. A large newsroom with a fleet of computers journalists use to open files from strangers all day will probably want that additional protection. Even so, that fleet of computers likely already has some built-in tools to address that risk.
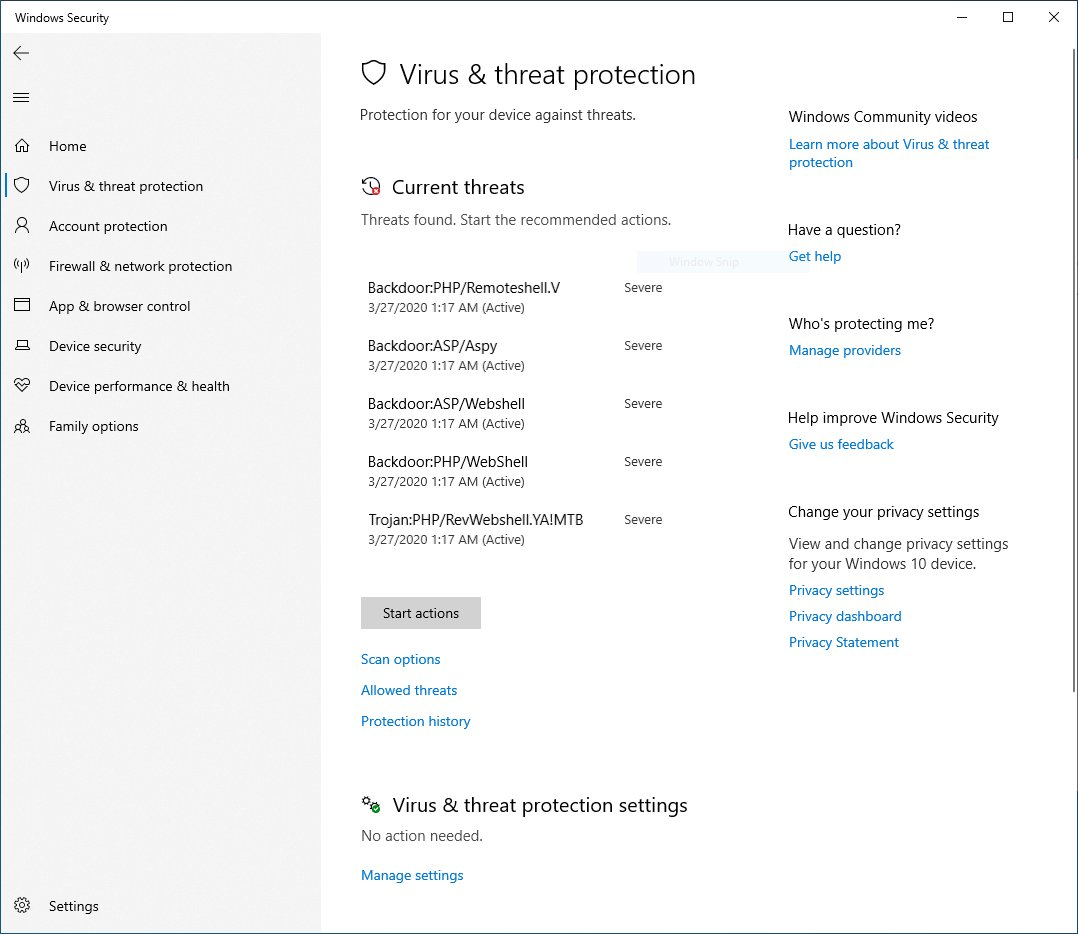
PCs running Windows 8.1, Windows 10, or Windows 11 have antivirus built-in. Windows Security, formerly Windows Defender Antivirus, offers most of the same antivirus protections one would get from third-party antivirus software out of the box, at no additional cost. Like other antivirus vendors, it includes a subscription to malware definitions, which they call "Security intelligence" and can be set up to perform different levels of scanning on-demand or on a schedule.
A modern Mac, on the other hand, uses a system called "Gatekeeper" which checks if apps you try to install are signed by Apple and came from the correct app developer, signaling that they are likely safe to use. If they are not signed, they may be blocked from being installed (although administrator users can manually make exemptions). Unlike antivirus, the approach front-loads the burden of checking for known malware in apps before they're distributed, and checks to make sure they haven't been altered between distribution and reaching your computer, to make sure that malware hasn't been added since their release.
Antivirus software sometimes includes additional features that go beyond malware detection and removal. Subscriptions may include additional features, such as data breach notifications, ad blocking, spam filtering, password managers and VPN services — all of which can be obtained separately from vendors that specialize in those features.
What about on my phone?
Antivirus is a little more complicated when it comes to mobile devices. On iPhones and iPads, iOS blocks the deep system access required to have full-fledged antivirus apps inspect each file in your device. However, those same measures help keep malware from having that same level of access, among other features that provide strong protections from malware making it into your device.
Android devices, on the other hand, have more variation on how apps, nefarious or otherwise, get on a device, how much apps can access, and how easily apps can be hidden. Regularly or automatically downloading and installing updates on your Android devices, however, does help protect them from most malware the same way it would on Windows or macOS.
Prioritize according to your own risks, not airport ads
Beyond these considerations, some malware doesn't always neatly fit the definitions the antivirus industry has historically considered, however. The rise of stalkerware, for example, is a sobering reminder that sometimes, nefarious software can be willfully installed by one user of a device to harm another user of the same device, and that's a reality the antivirus industry largely doesn’t address. More recently, however, organizations such as the Coalition Against Stalkerware have helped make progress against the proliferation of this particular strain of malware.
So far, Kaspersky, Malwarebytes, and Norton's Android offerings have features which can detect stalkerware. For iOS, security helper apps like the City of New York’s NYC Secure and iVerify are not antivirus software per se, but will detect some of the system changes that allow stalkerware to exist on the devices (such as jailbreaking). We hope to see other antivirus vendors follow their lead.
Ultimately, which security measures to adopt depend largely on the risks a journalist takes in their work and who they are to the world around them. Antivirus was originally intended to protect beige boxes designed for individual office workers in rows of gray cubicles with a dedicated IT staff maintaining them. Modern journalism includes people outside that model, such as people working from home, and you might be among them. Addressing password reuse, preventing phishing attempts, and adopting better smartphone security practices are more broadly relevant places to get started on leveling up your digital security.