Photo by WeissenbachPR. CC BY NC 2.0
So, you’ve been arrested covering an event. You’re taken to the police station, you’re booked, and your phone is confiscated. When you’re let out, after a few hours or even a few days, your phone is handed back to you in a plastic baggie, the SIM card and SD card taped to the back. Someone has definitely gone through your digital belongings.
What does it mean?
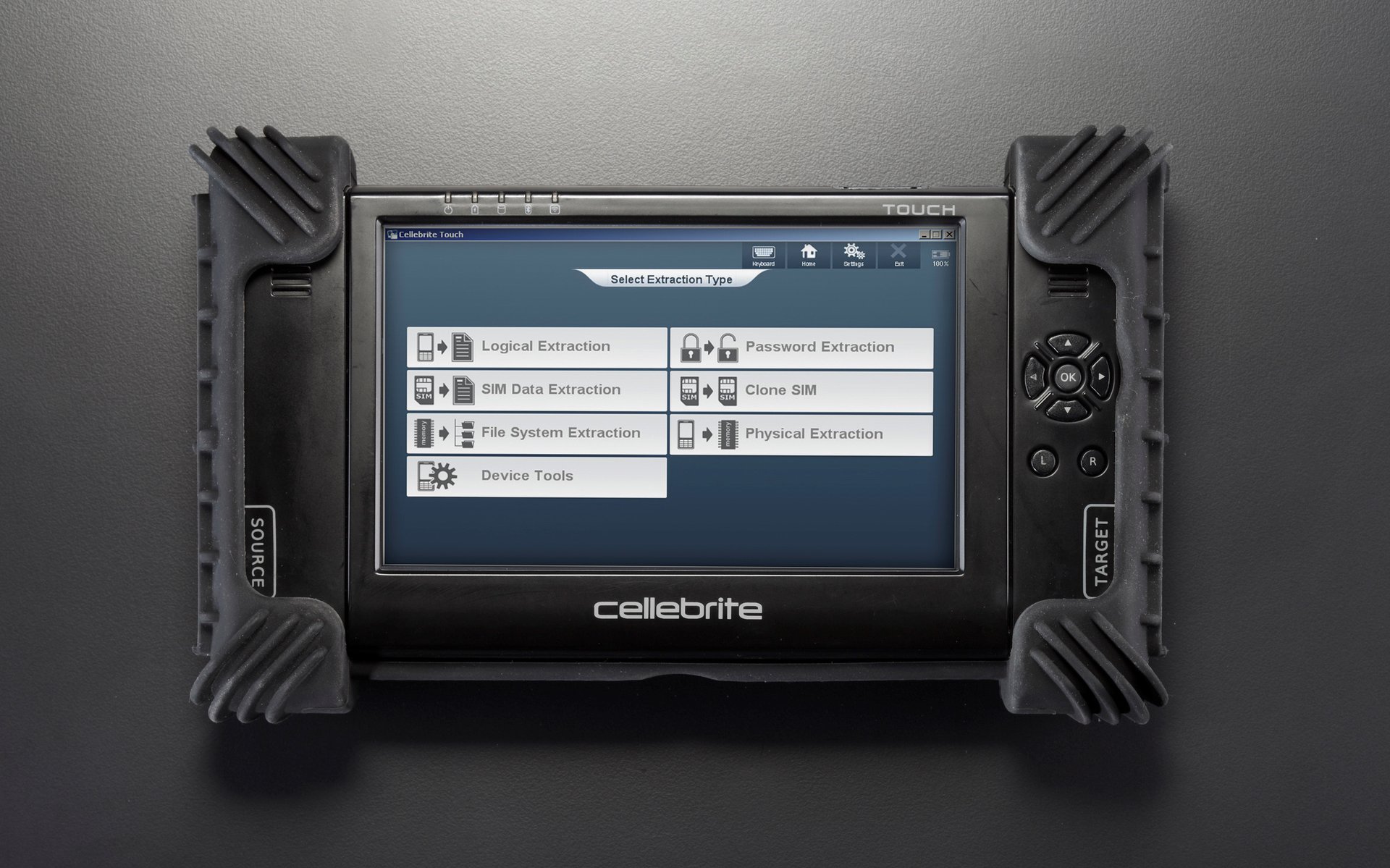
Your digital belongings — phone, SIM, SD card data — could have been copied and gone through.
Your phone may have been turned on, and apps and browsers opened. The cops might have access to any accounts your phone was logged into — this means they may have read personal communication, or noted your contacts' email addresses and social media accounts.
The SIM card contains very little information in modern smartphones but still holds your phone number and other numbers that uniquely identify it, sometimes printed on the card. Police may track the location of individuals through the location of their mobile phone and SIM card, and your unique phone and SIM combination may now be used to locate you.
The SD card contains photos and other media; it could also contain chat logs and other user-generated content. Not only can this data be used to build a profile on you but also to map social connections between people you frequently communicate with, who can unjustly become "persons of interest" to investigators. In addition, such tactics can be used, sometimes under the flimsiest of pretexts, to justify warrants for escalated surveillance on you in the near future.
What are your rights?
Depending on the circumstances of your arrest and the method of seizure of your mobile device, you are subject to a certain set of rights, laws, or protections. First off, know that in the U.S., it is your right to decline the warrantless search of your mobile phone. If you are arrested or taken into police custody, you should verbally state that you do not consent to a search of your devices. A law enforcement agency is only permitted to conduct a warrantless search of your device if a compelling case for an emergency can be made.
If you find that you are the victim of an unlawful search by police officials, you have various avenues for recourse:
- If the authorities are using evidence obtained through an unlawful search of your mobile device against you in a criminal proceeding, you can move for that data to be suppressed under the Fourth Amendment right to freedom from incidental seizures.
- If information gleaned from the warrantless and/or nonconsensual search of your mobile device is not used against you in a criminal proceeding, you have the right to sue the law enforcement agency or city for damages under Section 1983 of Title 42 of the U.S. Code.
- Were you arrested for recording or photographing the police? As a participant in a public event, you have the right to photograph and take video of law enforcement officers, but often documentation is taken, destroyed, or obstructed by law enforcement. If you are arrested for reporting on an event as either a credentialed or noncredentialed journalist, you may be allowed enhanced protections or alternative avenues of legal recourse. Professional journalists — as well as bloggers and livestreamers — have the right to document police activity at protests and demonstrations without undue state interference under the First Amendment right to freedom of the press.
What can you do?
As the saying goes, an ounce of prevention is worth a pound of cure. For the next time, follow these simple steps to keep your phone secure, your social media accounts safe, and your property out of reach from prying eyes. In addition to these tips, look at EFF’s excellent guide for protesters; it has great tips for how you can protect yourself next time you go out there!
- Make sure your phone is encrypted. Having an encrypted phone means that most data in that phone will not be readable to anyone when your phone is powered off. Even if a copy is made of your phone’s storage, it won't be readable without your unlock code. This requires using a PIN or passphrase to unlock your device. Speaking of which …
- Lock your phone. This might seem like a lot of work at first, but it's worth it, and you will get used to it. Check out our recommendations for phone unlock passwords. Change your settings so your phone locks immediately after a short period of time, say 30 seconds. While this doesn't encrypt your phone by itself (it's always unencrypted while it's on), it will prevent anyone from accessing and using your apps.
- Prevent your text messaging apps from showing the full text of a message while the phone is locked. No one should be able to read your communications with friends, or two-factor authentication codes, without opening the app first.
- Lock your SIM card. Set a PIN to control access to your SIM data and cellular network use. A SIM card may still be unlocked by your carrier, but locking it with your own PIN protects it from being used in someone else’s device unless they know that PIN. Note that when you first start this process, you will first need to enter the default passcode that is etched into your SIM card before you can enter your desired passcode. You might not know what that default passcode is and risk locking your SIM card after 3 incorrect attempts. So before you start to set up a SIM card lock, do a quick search online for the default PIN for your carrier. For example, Verizon’s default PIN is 1111.
- Protect your mobile service account. Take the time to properly lock down the account you have with your mobile carrier. It may seem like an afterthought, but it's possible for someone to take over your phone number and, eventually, all mobile communications if such accounts aren't secured. Use a long, unique password for your provider's website, as well as a long, unique password for the PIN or password used with customer service. A password manager will help create and store these securely.
- Keep a list of all the accounts that are important to you. Examples are accounts that need to have their passwords reset or that get logged out from all devices. In the event your device is compromised, it will save you time and worry.
- Burst the cloud! Frequently delete your browsing history from your web browsing apps via their settings. If you have a Google account, prune (or better yet, pause) your "Web and App Activity." If you use an iPhone, you should prevent messaging apps from syncing data to iCloud. We know it might seem scary, but unlinking your phone and Mac computers from iCloud is the best way to protect your data from anyone knocking on Apple’s door for it. Journalists, activists, and concerned citizens usually want to sync photos and videos to the cloud as soon as they take them and that's OK! If you can’t live without iCloud, enable Advanced Data Protection to prevent Apple from being able to read your backups. If you use an Android phone, consider using another cloud-based service that gives you more control over how, when, and where you sync your data. Paid services like Tresorit are end-to-end encrypted, meaning the service provider can’t read anything you back up.
If you find yourself in a situation where you’re very sure your device has been compromised, the first thing you’ll want to do is to preserve evidence.
- Keep your old SIM and SD card somewhere safe.
- Audit your account activity. From another, trusted computer, check your Google, Facebook, Dropbox (and other) account activity logs for activity that someone else might have generated while your phone was taken from you. Document any new IP addresses, locations, and devices by taking screenshots.
- Be on the lookout for strange activity in social media. Investigators have been known to try infiltrating your and your friends' networks with fake profiles, catfishing, (sometimes known as ‘catphishing’ in security parlance, or when a person who sets up a false personal profile on a social networking site for fraudulent or deceptive purposes) and other weird tricks. Get in the habit of documenting and taking screenshots of anything that looks strange to you.
Next, it’s time to regain control of your accounts and data. Follow these steps to restore your personal data and social media accounts.
- Sign out of all important accounts. Any place you’re logged into will have session cookies set somewhere, and an adversary could potentially resume your session if they've copied these cookies from your device. By logging out, you signal to the service that the session has ended.
- Refresh your device. At this point, you should either factory reset your phone or get a completely new one. While it's unrealistic for most people to buy a brand-new phone unexpectedly, it's also worth noting that the phone’s IMEI, or unique serial number, cannot be changed, even if you wipe the device and start from a fresh slate.
- Change the passwords for services you use. On another, trusted computer, reset each account with brand-new, complex passphrases. Additionally, if you enabled two-factor authentication on a particular service, that will also have to be reset. Instructions depend on the service, but nearly all services offering two-factor authentication will also provide a way to reset these codes.
- Get a new SIM. Your old SIM will be logged by authorities and might have had extra metadata pushed onto it while it was out of your possession. Get a new SIM card from your carrier by simply walking into the store. Remember, it’s your right to bring your old phone number with you, and it should be handled easily at the store. Be sure to bring two pieces of proper identification (driver's license, passport, Social Security card, etc.) because retailers require this proof of identity for customers' security.
- Replace the SD card. Purchase a new one, or use another one you already have (other than the one taken from you!). You cannot trust the old one since it's left your possession.
Who can I turn to?
When these things happen, it’s important to know who’s got your back. Finding legal representation that understands your situation, and understands technology, is key. You and your legal team might also require assistance from digital forensics experts or need to talk to digital security trainers who can help you navigate this tricky situation. Finally, self-care is hugely important. This work is extremely stressful; talking to the right people might help you recapture your courage, prevent you from doing harm to yourself and others, and help you get through the trauma.
Legal resources
- Your local affiliate for the ACLU: https://www.aclu.org/about/affiliates
- National Lawyers Guild: https://www.nlg.org/
- Law for Black Lives: http://www.law4blacklives.org
- Reporters Committee for Freedom of the Press legal defense hotline: https://www.rcfp.org/legal-hotline/
- Student Press Law Center legal hotline: https://splc.org/legalrequest/
Digital forensics
- Citizen Lab: https://citizenlab.ca/about
- Amnesty International Tech: https://www.amnesty.org/en/tech
Digital/operational security training
- Electronic Frontier Foundation: https://www.eff.org/issues/security
- Freedom of the Press Foundation: https://freedom.press/training/
- Access Now: https://www.accessnow.org/issue/digital-security/
- Safe + Secure (geared toward filmmakers): https://safeandsecure.film/
- Digital Security for Filmmakers: https://digitalsecurity.film
Mental Health Resources
- Dart Center for Journalism and Trauma: https://dartcenter.org/resources
- Committee to Protect Journalists (trauma support and preparedness resources): https://cpj.org/emergency-response/resource-center




