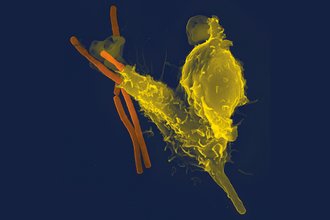
What about antivirus?
Antivirus software is one of the oldest offerings available from the now-billion-dollar cybersecurity industry. But what does antivirus software do to help protect our devices, what does it not do, and do we really need it?
Antivirus software is one of the oldest offerings available from the now-billion-dollar cybersecurity industry. But what does antivirus software do to help protect our devices, what does it not do, and do we really need it?

The choice between storing two-factor authentication codes on your device, versus a remote service in the cloud comes with some usability and security trade-offs.

Nearly everyone’s sent private photos at some point. But who else is able to see them, beyond your conversational partner? When sent over text messages and apps, who else gets a copy?If you send a photo over text message, the service provider (e.g., Verizon) can usually read the message …
Before potentially burning a source or tipping off a target before you're ready, journalists should know the privacy and security constraints of email — who can see your emails, and when?

Also available in Spanish.Passwords are the brittle wall that keeps unwanted visitors out of your accounts. When it comes to account protection, two-factor authentication is one of the most effective defenses available.Two-factor authentication, or 2FA for short, strengthens login security by requiring a second piece of information …

One of the most common questions we get in training journalists on two-factor authentication (2FA) is: How hard are these hardware security keys exactly? Our digital security team has plenty of anecdotes to support their durability, but we've decided to methodically put them to the test.

Once upon a time, Microsoft Office provided a small suite of applications on your computer, including Word for writing, Excel for spreadsheets, and PowerPoint for presentations. But increasingly, modern newsrooms use Office 365 to access these tools over the web, alongside remote storage and team management software. While working on the web offers obvious advantages, many reporters also wonder about the privacy and security of this data. What about our most sensitive, unpublished details when reporting? What can Microsoft see?

Freedom of the Press Foundation and the University of Southern California Annenberg School for Communication and Journalism are excited to announce an innovative partnership to develop comprehensive digital security education for journalism and communication students. Additionally, Yubico, a leading provider of hardware authentication security keys, will be providing YubiKey …

This guide is an overhaul of a previous piece, entitled "Encrypting email with Mailvelope: A beginner's guide."

Thinking about securely leaking information to news organizations? This guide will show you how.

If you work in a newsroom, there’s a good chance you work with colleagues on Google Docs, Slides, Sheets, and more. Google Workspace software is simple and powerful. But anyone working in a newsroom has probably asked themselves: What can Google see? What about our most sensitive conversations and documents? What about documents that concern our own unreleased reporting, or information on our sources?

Last week, Eric Trump tweeted a screenshot of an email that circulated through the Trump Organization by Washington Post reporter David Fahrenthold. Although the tweet sensationalized Fahrenholt’s emails, it should fall short of qualifying for reality TV levels of drama, since reporters do this sort of thing all the time. But are there other considerations to take in mind when reaching out to sources in their workplaces?

An ever increasing amount of traffic flows through our devices, turning web browsers from our primary gateway to the web into our primary gateway to the rest of the world.In the early months of the COVID-19 pandemic Google Chrome delayed expected browser updates, as employees quickly transitioned to …

This guide is intended for readers familiar with using PGP who want to take an extra step in fortifying the security around their private key. Some of these steps also utilize a command-line interface, and it may be helpful to get comfortable with that interface before diving in. For a …

Journalism schools have been slow to offer comprehensive security education to students. What's getting in the way?

The Digital Security Training track currently offers a variety of courses covering the most salient and pressing issues facing journalists and technology in the current day. FPF offers courses in 90-minute, 3-hour, and full-day formats; in order to accommodate organizations requiring for more flexibility in scheduling. Some courses include hands-on …

They are tethered to wireless networks, and we are tethered to them. We spend so much time with smartphones, yet most of us devote little of it contemplating our small computers. We often treat these valuable devices more like everyday household items, as opposed to curated archives of our lives. …

If your web browser is asking you to install software updates, it may also be asking you to protect itself from getting hacked.

Data breaches, and in particular those including personal passwords for websites or apps, are evergreen news stories that repeat themselves like an Advent calendar for cybersecurity failures. Although these breaches are a regular phenomena, they are trailed by a long, drawn-out window of time where other attackers use breached data …

Proton Mail is a Switzerland-based email client that offers end-to-end encryption between its users by default. This means that communication between anyone whose email is managed by Proton Mail can only be viewed by members of that party; No outside parties, including Proton Mail itself, can view the content of …

This piece is a part of a series of guides about encryption for media makers; take a look at the full collection here. We recommend you review our introduction to encryption piece for pro-tips and a technical glossary before proceeding with the step-by-step instructions below.Looking for …

No matter who we are or where we work, each of us has information to keep secure and private. For media makers working in film, journalism, and the arts, data protection is essential. Audio, video, image, and text files make up the bulk of their work, and their livelihoods. The …

This piece is a part of a series of guides about encryption for media makers; take a look at the full collection. We recommend you review our introduction to encryption piece for pro-tips and a technical glossary before proceeding with the step-by-step instructions below.VeraCrypt not …

This year we're gifting simple security guidance, which I think we can all agree is better than another internet-connected kitchen appliance.

Most sources don’t reach out with terribly sensitive information. But sometimes they do.