
Discord boosts private call encryption
Discord announced its rollout of end-to-end encryption for voice and video calls in one-to-one and group direct messages, voice channels, and Go Live streams.

Discord announced its rollout of end-to-end encryption for voice and video calls in one-to-one and group direct messages, voice channels, and Go Live streams.

We’ve heard some questions about the difference between Signal usernames, phone numbers, profile names, profiles, and nicknames. Let’s talk about it.

FPF's digital security advice column today answers, why should I trust Signal?

Apple has filed a motion to withdraw a lawsuit against NSO Group, an Israeli spyware company.

No need to break the bank when your newsroom sets up its first tipline or drop box.

Following the arrest of Telegram founder and CEO Pavel Durov, the messaging app modified its FAQ page to clarify some new rules.

FPF's digital security advice column today answers, what happens if I lose the phone I use for two-factor authentication?

Columbus Mayor Andrew Ginther announced that the data was either “encrypted or corrupted.”

Apple has released numerous security and privacy features over the past few years. If you use iCloud, you’ll want to enable Advanced Data Protection.

The arrest of Telegram founder Pavel Durov has helped foster the mistaken notion that the app is a standard end-to-end encrypted messenger.

Are you a journalist with a question about digital security? Ask our team!

FPF's digital security advice column today answers, what are your top three security tips?

National Public Data confirmed nearly 3 billion records were affected.

Protecting sources from harm should be the top priority of any newsroom. Whistleblowers risk identification when sending confidential files over mainstream email and messaging services. Although there are many secure file-sharing applications, they vary in cost and technical expertise.OnionShare, a free file-sharing application, makes it easy to send and …

The latest move means that the app has been removed from Google Play and Apple App Store in Russia.

The Spamhaus Project has released a blog criticizing Cloudflare — a content delivery network and cloud cybersecurity provider — for providing security services to abusive domains. These websites could contain spam, phishing links, malware, and even botnets.

No matter what happens this November, spying on members of the news media may be an ongoing problem

The cybersecurity firm Kaspersky disclosed that at least five Google Play applications contained Mandrake, a sophisticated cyberespionage tool.

Google has a habit of hitting the brakes on products and features — so much so that it’s become something of a meme to be “killed by Google.” This time it decided to backtrack on its long-standing plan to replace traditional tracking in its Chrome browser.

Last Friday, computer systems worldwide were taken down by a defective update from enterprise cybersecurity vendor CrowdStrike. In the wake of the outage, the U.S. Cybersecurity and Infrastructure Agency is warning of phishing emails, with attackers posing as CrowdStrike customer support.

Most note-taking applications have limited security and privacy features. Here are some alternatives you could adopt for your newsroom.

Around 110 million AT&T subscribers were affected by a data breach from May 1 to Oct. 31, 2022, TechCrunch reported.

We can learn a lot about how to get ahead of these problems.
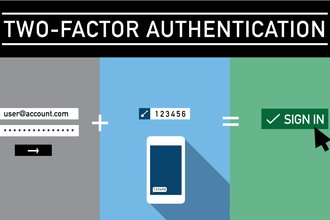
The parent company for Authy, an application for two-factor authentication, has issued a critical security update to its Android and iOS users. According to BleepingComputer, hackers utilized leaked phone numbers from past data breaches to identify up to 33 million Authy users.
Apple released a firmware update patching a critical Bluetooth vulnerability in AirPods, AirPods Pro, AirPods Max, Powerbeats Pro, and Beats Fit Pro. According to its support page, an adversary in Bluetooth range could spoof as an intended source device for these wireless headphones. When the targeted headphones send a connection request to the spoofed device, it could eavesdrop on confidential conversations.