Wipe your own code … Now with agentic AI!
AI agents are a bit like eager interns — they still need intentional management and supervision
AI agents are a bit like eager interns — they still need intentional management and supervision

Okay, this is really the last thing we need right now

Spoiler alert: This also applies to incoming notifications for every app. Learn how to adjust your settings

It may be a problem sooner than experts think

Lawmakers sent Tulsi Gabbard a letter asking for clarification about how the use of VPNs affects Americans’ privacy rights
The best time to update your devices is all the time

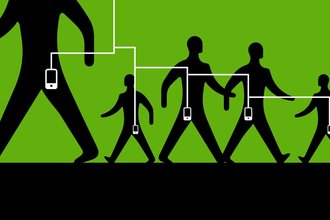
Using advertising infrastructure, Customs and Border Protection can track users’ locations when targeted devices are served ads

A recent story of a Proton Mail user unmasked for Swiss authorities highlights what the company can and can’t protect
Intellexa founder and three others found guilty of using mercenary spyware to target journalists and senior government officials in Greece

FPF’s Harlo Holmes offers advice on 404 Media podcast

Lockdown Mode is not just for dealing with remote malware — it also appears to shut down some forensic devices.

We’re showing our favorite digital security tools some love in our newsletter this week. Read up on why we love security keys.

Let’s appreciate all that passcodes do for us by sending this week’s Valentines to them and their natural home, the password manager.
As heart-shaped chocolate boxes fill store aisles, allow us a moment to write a love letter to one of our favorite tools: Signal.
Confer is an open source, end-to-end encrypted chatbot.

If you got one of these emails, you weren’t alone.

Even if you don’t live in the Golden State, there are things you can do to opt out of invasive data broker companies.

How might Chrome put guardrails on AI ‘agents’?

The Pentagon inspector general’s report gives more details on the incident than ever before.

To protect your sensitive conversations, you’ll need to make sure your device is safe.
Researchers discovered phone numbers and, in some instances, associated profile photos and names through WhatsApp’s contact discovery tool

Data breaches are an unfortunate fact of modern life. While we can’t always control the security of the apps and services we use, there are some steps we can take to limit how much of our data is out there.

The names, email addresses, and chat histories of over 17,000 employees and external business contacts in the company’s Slack system were exposed thanks to one infected computer.

Despite their growing presence, AI-powered browsers aren’t ready for prime time when it comes to security
Online scamming has become an industry.