Privacy-conscious Internet users were aghast last week when court documents showed that Microsoft looked at the content of a blogger’s Hotmail account without a warrant—or any legal process whatsoever—in an attempt to root out a employee within Microsoft who was allegedly leaking the source code of Windows 8.
The move was widely criticized as both a violation of privacy and press freedom. As privacy law scholar Jennifer Granick told the New York Times, “What blogger will use [Microsoft’s email service] now?”
But while Microsoft is rightly taking the brunt of criticism, the episode exposes a long-brewing, much larger problem for journalists and news organizations: many of them are outsourcing their email to third-parties and are losing their legal rights by doing so.
It’s Not Just Microsoft
Many users found out for the first time thanks to this scandal that Microsoft’s terms of service allow for the company to read your email in a host of situations. As EFF points out, they can do so not only to “protect their rights and property” but if you violate their “code of conduct,” which includes using profanity or sending pictures containing nudity. But Microsoft is not unique here: Google, Apple, and Yahoo all have clauses in their terms of service that allow them to read your email with no legal process if they are protecting their “rights or property” as well.
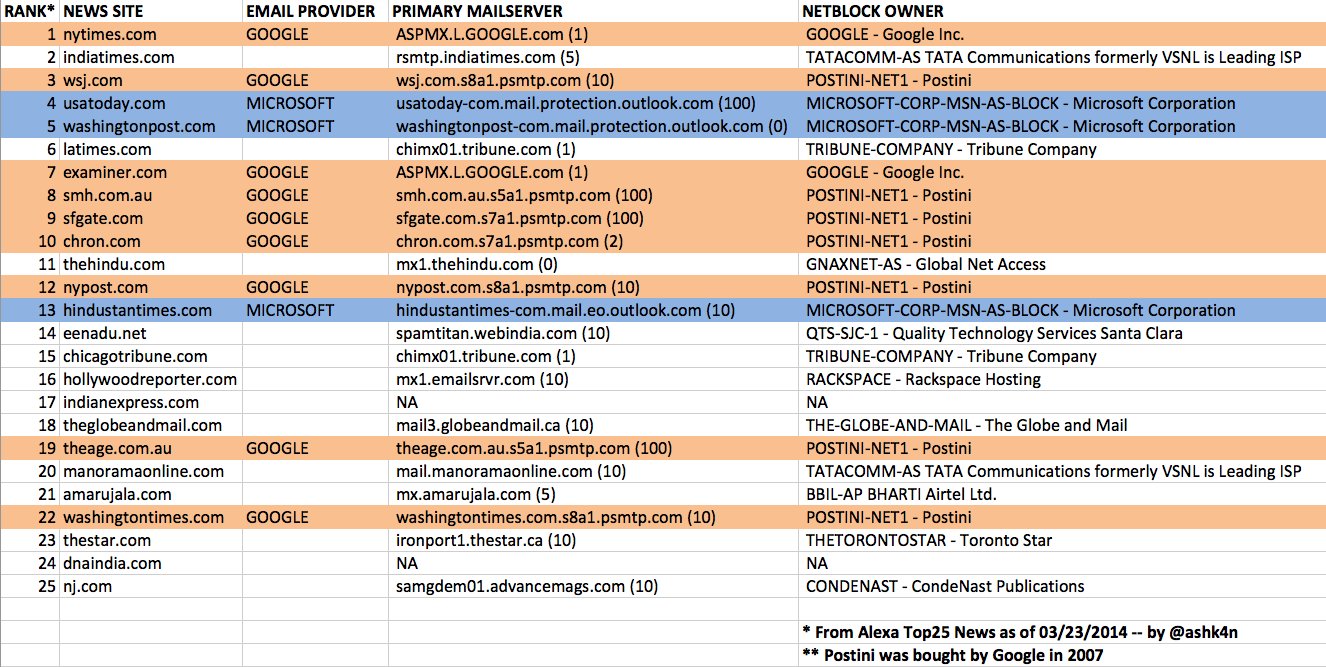
Yesterday, independent security researcher Ashkan Soltani looked at the top twenty-five news sites on the Internet and almost half—12 out of the 25—used either Google or Microsoft to host their email instead of hosting it themselves.
This puts any tech journalist covering the major tech giants at risk if they cover the same company that provides them with email, and potentially if they cover the company's competitors as well.
Soltani wrote a Python script that scraped email providers of the largest news organizations on the web, but if you want to check a specific organization, you can do it yourself: just open a terminal, type “dig +short mx” plus the domain of the news organization and then hit enter.
This is not something we should have to expect from sources every time they want to email a reporter something sensitive. News organizations have to be better than that.
Third Party Providers Lead To Leakers Getting Caught
While the Microsoft case was particularly egregious, we’ve known of a similar “third party problem” for a while now in the national security context. If there is one overarching reason why the Obama administration has been able to prosecute more news sources than any other administration in history, it’s because emails or phone call records are held by third parties. Instead of being forced to call reporters to testify in court (where reporters will frequently refuse to comply to the point of going to jail), the government figured out it can just subpoena third parties and journalists won’t know their communications are in the hands of the government until it’s too late to legally challenge it.
If you look at the cases of Thomas Drake, John Kiriakou, the Fox News case, or the AP phone records case, you will see the government never tried to call the reporter to testify, they just took emails or phone records held by a third party.
This isn’t just a worry for national security reporters: Remember, one of the biggest reporter’s privilege cases in the past decade involved two baseball journalists reporting on the BALCO grand jury investigating steroid use. Now it’s clear it affects tech reporters as well.
Alternatives
We will admit running your own email server is not an easy decision for news organization. Many use Google because they have a team of three hundred people working to keep Chinese hackers out of their email system. This is something no news organization can match and it’s a legitimate problem: the nation’s biggest papers, including the New York Times, Washington Post, and Wall Street Journal, have all had their entire networks allegedly compromised by hackers in China. Google also has a variety of additional phishing preventions and alert systems that news IT teams may not be experienced in handling.
“News orgs are stuck between a rock and a hard place. Arguably cloud services like Google provide better against outside attackers than small IT departments," Soltani said. "However these services offer far less privacy than self-hosted solutions, especially when the Terms of Services allow snooping of user’s emails. There's a significant tension between privacy and security – with very few options for these companies.”
There are a number of projects attempting to solve the secure-email problem (outlined here), but none seem ready for prime time unfortunately.
The court documents in the Microsoft case also showed how they accessed the blogger’s chats with the alleged leaker, exposing a similar problem of relying on a third party chat service. The Intercept runs its own Jabber server, which partly eliminates the third party problem and also makes it easier for their journalists to encrypt more of their chats. But this is an exception—not a rule—to newsrooms, and running your own Jabber server is not an easy task either.
SecureDrop, our open-source whistleblower submission system, tries to eliminate the third party problem altogether—SecureDrop servers sit solely on news organization’s property and there’s not a third party provider the source uses either. All of the data is sent to the one server owned by the news organization. But for regular communication, using SecureDrop is cumbersome, and can’t solve the problem for an entire newsroom.
Ultimately, news organizations just may need to invest more money in their own email systems and hire more security so they can get the benefits of both the technical and legal privacy protections.
But the bottom line for news organizations is: If any of your journalists report on leaked material, they are losing legal rights by not hosting email yourself.
Note: Ashkan Soltani is a member of Freedom of the Press Foundation technical advisory board.