
“Onion services,” a technology offered by Tor to ensure users can securely and privately visit particular websites, can provide a major step forward for readers who rely on the Tor network for its privacy and censorship-resistance properties. Today, we’re adding onion service tracking to our Secure The News scorecard, which has already tracked the adoption of other encryption technology—namely, HTTPS—by news organizations since 2016.
Since that time, we’ve seen news orgs make massive progress. Only 29% of tracked sites were offering HTTPS when we began, compared to 97% of news organizations today. (If your news organization is one of the few not yet serving your site over HTTPS, we’ve provided resources for why you should do so, and how you can set it up.)
Onion services are certainly at the beginning of that curve, and have to date only been deployed by a handful of outlets. But we hope and anticipate that will improve in the coming months and years, because the Tor anonymity network is a critical privacy technology for sources, journalists (it is what powers our whistleblower submission system, SecureDrop) and their readers.
To understand the role onion services can play, it helps to have a general understanding of how they work. An onion service is an address that can only be accessed via the Tor anonymity network, usually using the Tor Browser instead of Chrome, Safari, or Edge. These addresses look like very long jumbles of letters and numbers that end in .onion.
Some sites are only accessible as onion services, either because the site operator wants to preserve their own anonymity, or because they want to guarantee that readers take the precaution of accessing the site over the Tor network. SecureDrop instances, for example, are only available through Tor.
For news sites, an onion service address allows readers to access the site securely, with the entire connection running within the Tor anonymity network. That end-to-end Tor connection ensures strong reader privacy for readers, and the use of Tor enables users to circumvent some forms of network censorship.
In addition, by using the onion service instead of the regular site, the traffic load on Tor exit nodes is reduced (a “node” is a volunteer server that routes traffic through the Tor network, an exit node is where Tor traffic combines with the regular internet). This frees up bandwidth for other folks using Tor to protect themselves.
Beyond news outlets, a large and growing number of major sites from Cloudflare to DuckDuckGo to Facebook now provide onion services for their users, alongside traditional web addresses. This is good news for users of those sites that are especially privacy conscious or need to circumvent censorship.
On Secure The News, we scan using the Onion-Location header. This header as of Tor Browser 9.5 will promote the onion service to Tor Browser users. Clicking on the “.onion available” icon in the URL bar below will redirect the user to the onion service for that site:
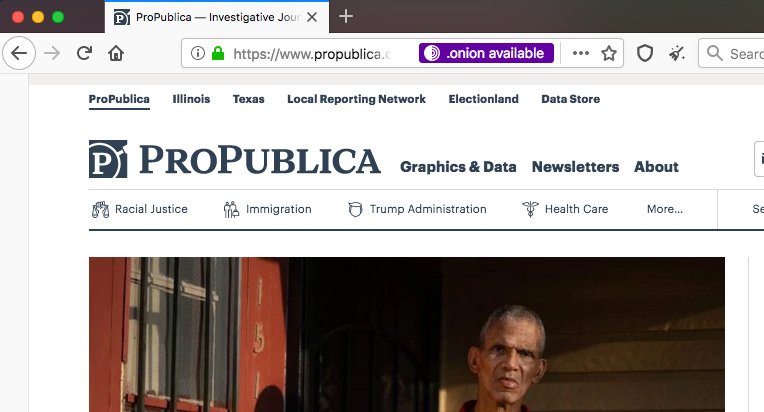
Currently we have just four news organizations providing an onion service for their main site and advertising it using the Onion-Location header: The New York Times, Propublica, Deutsche Welle and taz.de.
If you are interested to learn more, see the Tor Project page on how to add an onion service for your readers. You can also check out Alec Muffet’s Enterprise Onion Toolkit project. Tor has also provided information about how to add the Onion-Location header to a site’s server configuration.
We’re always looking for ways to promote security improvements to protect readers. If you have ideas of security improvements you would like to see Secure The News track and advocate for, please let us know!




