Over forty news organizations use SecureDrop, including the New York Times, Washington Post, Pro Publica, the Intercept.
As the true nature of Donald Trump’s reasons for firing the FBI director come to light, it’s clear that leaks and whistleblowing have never been more important to investigative journalism. But getting that essential information to the press can be risky.
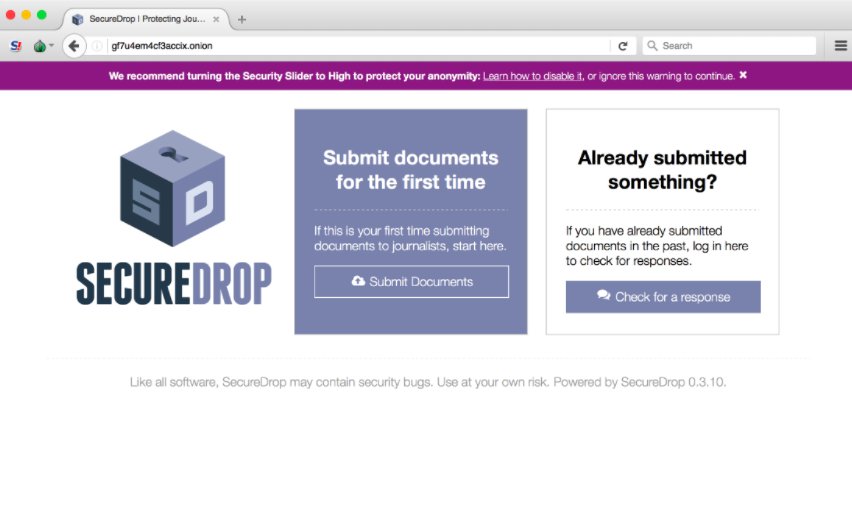
Sources can use SecureDrop, our open source whistleblower submission system which is now in over forty major news organizations worldwide, but there’s still the challenge of making sure readers and would-be whistleblowers know that news organizations support it.
If you work for the Trump administration and your conscience compels you to blow the whistle, you can use @SecureDrop to contact the press. pic.twitter.com/Pen7JFAMBC
— Freedom of the Press (@FreedomofPress) March 22, 2017
Some organizations have SecureDrop links on their front page, or links to instructions for sending in secure tips. But news organizations can take an additional step to get SecureDrop instructions in front of the people who most need to see them. To demonstrate how it can be done on Twitter, we designed an advertising campaign last month that specifically targeted EPA and NOAA employees in the Washington, D.C. area, urging them to leak newsworthy documents to one of the dozens of news organizations that currently use SecureDrop.
Ours is not the first such effort. The investigations team at Gizmodo Media Group recently announced that it was running targeted Facebook ads at government employees in Washington, D.C., imploring them to visit their SecureDrop landing page at TellOnTrump.com. In the interest of transparency, we wanted to see if we could do the same thing on Twitter — Trump’s preferred platform — and lay out the steps for news organizations who want to follow suit.
Below, we describe how we went about targeting potential whistleblowers with advertising. We are providing these instructions so other news outlets can run a similar campaign. Any news organization can do this, whether they are interested in whistleblowers from inside the government, corporations like Facebook or Uber, or any entity in between.
How we created a Twitter ad for potential whistleblowers
In our case, we chose to target employees of the EPA and NOAA that work at the headquarters of each agency in the Washington, D.C area. Fortunately, each of these organizations, like many public agencies, makes a directory of its staff available to the public. Neither agency’s search service would show the full list of employees, but it’s straightforward to craft a set of search terms that will eventually produce the full list. By doing that, we were able to create a directory of thousands of names of employees.
This marks our first data integrity issue: our list of employees is only as good as the publicly available staff directory. If targeting integrity is more important for your purposes, it might be possible to procure an updated list through a FOIA request or an internal directory.
We knew that we could use Twitter’s “tailored audience” feature to serve an ad to a list of known usernames. So as our next step, we sought to find the Twitter accounts of employees who use the service. This is more art than science, but we had a concrete goal in mind; the “tailored audience” feature requires at least 500 accounts.
Armed with our list of names, we wrote a script to search Twitter for matching accounts and then filter for those who had “EPA” or “NOAA” in their bio or provided a location in or around Washington, D.C. This approach produces some false positives — other District residents with the same names as EPA employees, for example — but the cost of those false positives is small, so long as the intended targets are presented with the message.
Again, if narrowly tailoring the targets is more important for your purposes, you could start with known Twitter accounts and step through their follower graphs. If you want to cast a wider net, you could target the followers of a given account, or “lookalikes” for a set of known employees. For our purposes, the broad cross-section provided by searching for names and filtering by location and bio text is appropriate. We ended up with about 700 names.
Finally, we needed to create the message to serve to the potential leakers. We wanted to communicate the value of leaking and provide information to interested employees, all in a way that keeps prospective whistleblowers as safe as possible. To that end, we decided to use a little bit of text inside a photo to tell people to use their own computers on trusted networks to download Tor and access the SecureDrop directory, and we decided not to include a link that might tempt them to do otherwise.
Newsrooms or journalists could craft more specific messages. Similar campaigns can also be run on Facebook or other social media services. Our campaign, as a proof of concept, didn’t need to do that. Our aim was to ensure that those government employees who cannot ignore their conscience’s directive or their patriotic duty to blow the whistle know that there are (relatively) safe options available to them.




