An ever increasing amount of traffic flows through our devices, turning web browsers from our primary gateway to the web into our primary gateway to the rest of the world.
In the early months of the COVID-19 pandemic Google Chrome delayed expected browser updates, as employees quickly transitioned to working from home. Browser vendors were forced to delay plans to deprecate insecure protocols after realizing it could prevent users from accessing critical health and government websites. And while these delays impact the rollout of technologies embedded in our browsers, their trajectories have not fundamentally changed.
Google continues to hold a dominant share of the browser market. Back in 2019 Google made headlines for its controversial plans to change how extensions will work in Chrome, with potential to undermine the efficacy of ad blocker extensions. Those plans are still in motion. Google is also testing tools for interest-based ad targeting without cookies, just as many other popular browsers have been phasing out trackers, particularly through third-party cookies.
Whichever browser you use, it may be a good time to look at what features browsers have to protect your privacy and security online — maybe even re-evaluating your browser of choice.
The browser you use has a real impact on your safety online: alongside advertisers tracking your online activity, there are also adversaries who may try to exploit bugs in your browser in order to compromise your entire system (regardless of which browser you do choose, it’s always important to ensure you have the latest update).
There are quite a few options across various operating systems and devices, so it can be difficult to determine which one is right for you. We’re looking for browsers that provide good network security, protect your privacy, and maintain the user experience you expect. Note we are only looking at browsers that will work on all major platforms, and not those that require a specific platform, such as Apple's Safari.
Tor Browser
Platforms: Windows, Mac, Linux, Android
Maintainer: Tor Project
Tor Browser is the best option when it comes to safeguarding your privacy, though it's important to understand its tradeoffs for routine browsing. This hardened version of Firefox is designed to protect user privacy by reducing the amount of unique bits specific to your browsing experience. By limiting the amount of browsing data you share with third parties, Tor Browser effectively prevents trackers from uniquely identifying or fingerprinting you.
Websites and the ads embedded in them use trackers to try and collect as much information as possible about your browser, such as installed fonts, screen size, operating system and version, or plugins, to identify you across multiple websites. This technique is known as “fingerprinting.” Instead of maintaining a list of trackers to block, Tor Browser aims to disguise the unique information about you, for example by using a common set of fonts, using a standard window size, faking platform information, and using a consistent set of plugins. While trackers can figure out that you are using Tor Browser, you’ll appear the same as any other Tor Browser user.
All network traffic runs through the Tor network, an anonymity network designed to conceal your location and IP address. Requests to websites that support HTTPS are automatically converted to use the more secure protocol. One caveat: Depending upon its popularity in your region (the Tor usage by country statistics can help you get an estimate), Tor users may actually draw attention upon themselves in regions with low Tor usage.
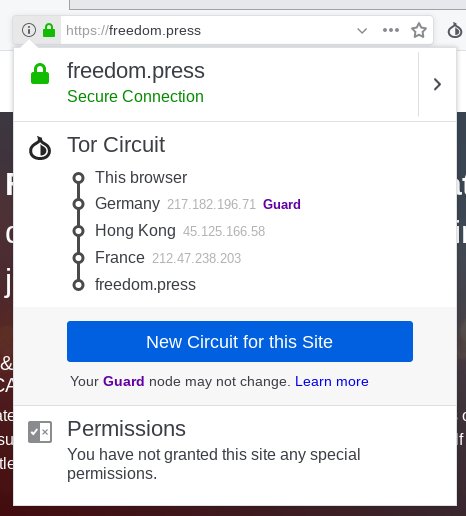
Each tab you open on the Tor Browser creates a new circuit, routing your requests to multiple servers throughout the world.
On top of that, Tor Browser allows users to strengthen its security by toggling through progressively more robust security settings. Users with the highest security settings enabled be warned — you may have to contend with decreased functionality on some websites you visit, especially those that rely heavily on JavaScript. Tor Browser also “sandboxes” requests, isolating processes within the browser to mitigate the impact of vulnerabilities. However, this isn’t available on all platforms yet.
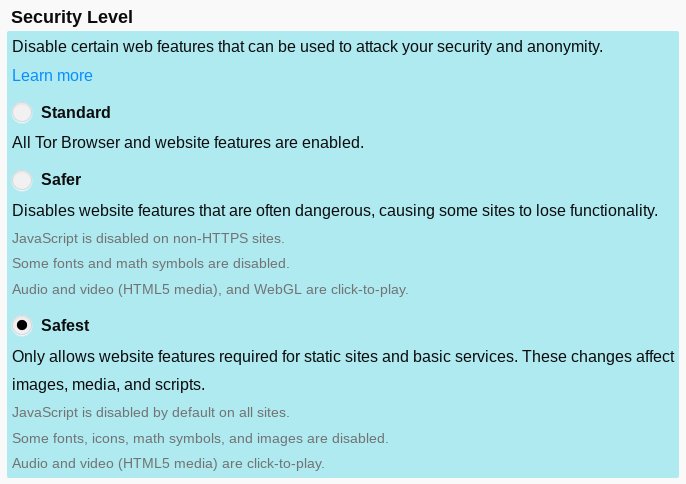
The three levels of security settings offer users the choice to toggle between different browser experiences.
Each separate website you visit is isolated from others, so tracking cookies cannot follow you as you browse, limiting advertisers’ ability to build a profile on you. These “third-party” cookies are set when a website operator uses an external service to provide extra functionality, usually ads or analytics.
These privacy-enhancing features come at a cost though. Tor Browser won’t keep you logged in to websites or store history between sessions, and discourages customization of the browser. You’re more likely to hit CAPTCHAs, and popular streaming services like Netflix won’t work. Interactive features that websites utilize may be disabled to prevent them from revealing too much user information.
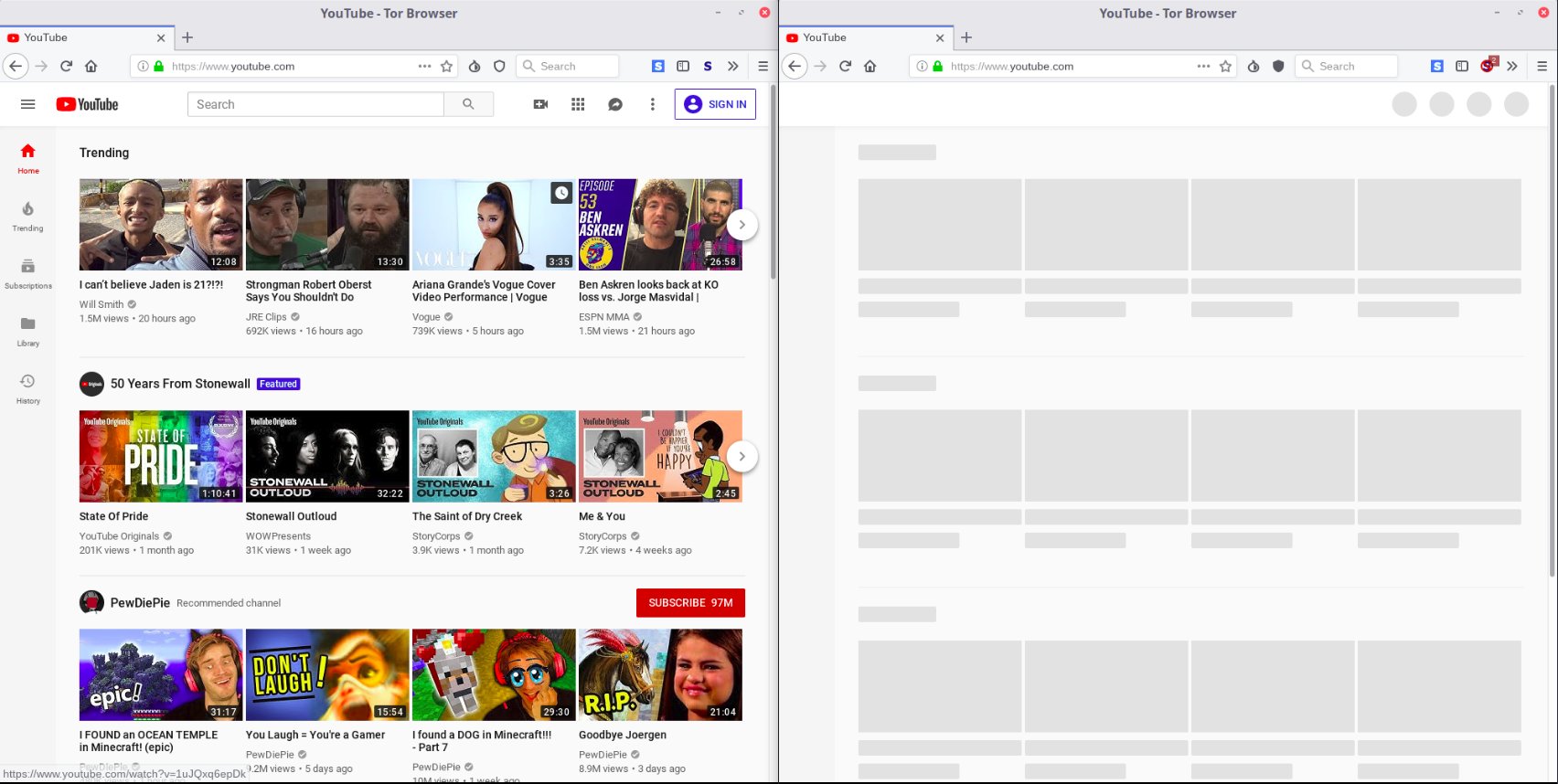
Tor Browser on the “Standard” security level (left), and on the “Safest” security level (right).
All told, Tor Browser is an incredibly useful tool for risky research, private communication, and censorship circumvention that should be part of your toolkit, but is unlikely to be an appropriate tool to use as your daily driver.
Firefox
Platforms: Windows, Mac, Linux, Android, iOS
Maintainer: Mozilla
Firefox provides a straightforward user experience, and takes steps to protect users’ privacy by blocking known trackers. This approach, while not as strong as Tor Browser’s anti-fingerprinting measures, is significantly better than nothing. And over time, privacy-enhancing features from Tor Browser are making their way into standard Firefox.
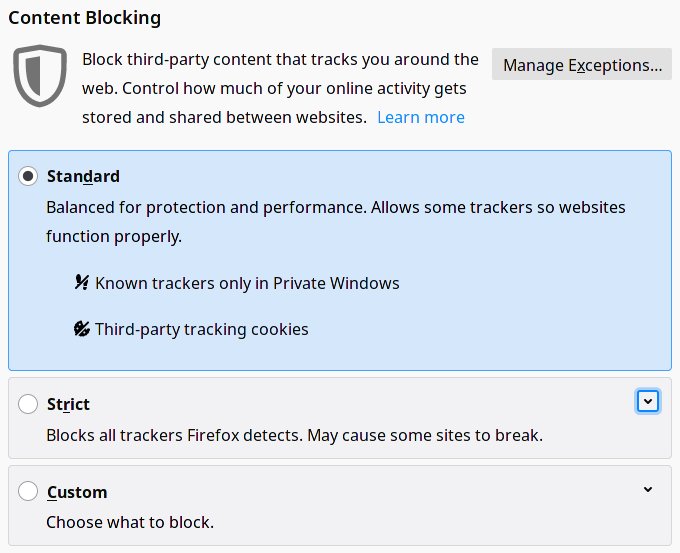
Firefox features strong privacy enhancements to your browsing experience in its "Standard" settings.
For stronger privacy and security, users may need to install a few additional browser add-ons. For example, users may also want to install uBlock Origin and Privacy Badger, other ad/tracker blockers with access to even more tracker block lists.
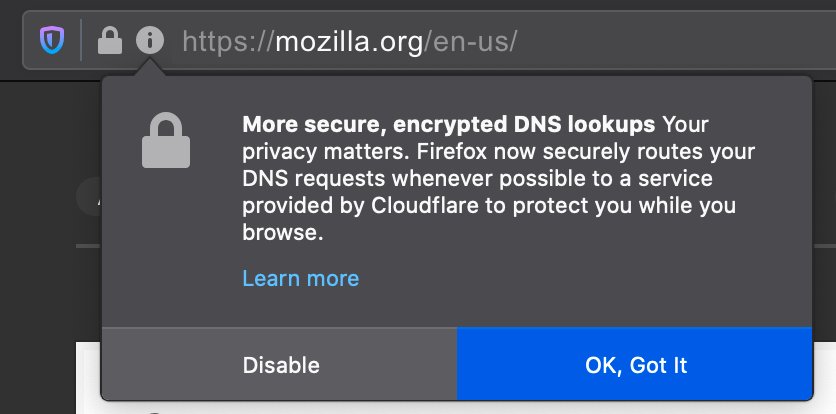
Firefox will prompt users to encrypt domain name lookups using the DNS-over-HTTPS protocol.
Firefox uses a feature called DNS-over-HTTPS to protect the records of your visits to websites. Much like a phone book lists a person’s name and phone number, we depend on a routing system called DNS, which is responsible for translating domain names (e.g., https://freedom.press) to server IP addresses (e.g., 104.22.23.122). DNS connections have traditionally been unencrypted, allowing your Internet service (e.g., Comcast) provider to snoop on the websites you visit. DNS-over-HTTPS secures these requests by encrypting them with the commonly used HTTPS protocol. Taking it a step further, Mozilla requires all DNS-over-HTTPS providers contractually agree to delete any user data after 24 hours and not sell or distribute that data, on top of other restrictions.
Firefox features “containers,” which allow you to fully separate different profiles and accounts. If you wanted to log into a website with two different accounts, you could have a container for each account. The containers are fully isolated from each other, so if you visited your bank’s website in one container, and did some shopping in another, no local data (e.g., browsing history, cookies) would be shared between the two.
Firefox continues to make enormous strides on blocking tracking cookies, often used by marketers to mine users' activities for targeted ads. The browser tries to block third-party tracking cookies by default using a predetermined list of trackers. Firefox also confines cookies to the website where they were originally loaded, preventing websites from being able to track users on unrelated pages. Firefox has also made tracking harder by isolating files loaded across websites, which are sometimes used to recreate a user's identity even when cookies are deleted. And if you want to delete history and cookies for any website, Firefox also allows users to make the browser "forget" specific entries in browsing history, alongside all associated cookies and files. It's clear the team is putting a great deal of care into making online harder.
Firefox also provides an end-to-end encrypted sync feature, that allows sharing bookmarks and history across multiple devices, including between your desktop and phone— without giving that data up to Mozilla or third parties.
In terms of security, Firefox continues to see major improvements in its sandboxing implementation across all platforms and is experimenting with new strategies to make browsing the web safer. Recently it has deployed Site Isolation, which makes it harder for malicious websites and trackers to access data from other websites you visit. This feature has been available in Chrome since 2018, and it seems Firefox is closing the gap.
When browsing on a mobile device, also consider trying out Firefox Focus, a lightweight browser with a tracker blocker that deletes history once you’re finished browsing.
Brave
Platforms: Windows, Mac, Linux, Android, iOS
Maintainer: Brave Software
Brave provides a hybrid user experience, offering similar measures to Firefox to protect your privacy, while keeping Google’s Chromium security features. By default, it blocks known ad trackers and upgrades requests to HTTPS if possible.
Brave is designed to communicate what measures it takes to protect your privacy, with blank new tabs displaying how many ads and trackers have been blocked.
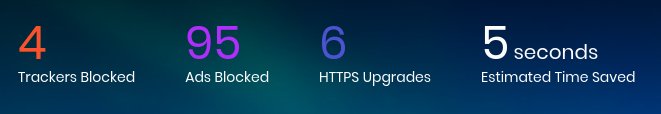
Brave offers users real-time metrics on ad and tracker blockers, and usability features.
It also allows further anonymity by opening a private Tor window that routes most network traffic over Tor. While using Tor will likely improve your privacy, the protection offered by Brave is not as fully-featured as the hardening provided by Tor Browser, and could potentially leak information that would have normally been protected by Tor Browser. For example, Tor Browser uses a technique known as letterboxing to prevent trackers from determining your screen size; Brave doesn’t support that yet. On top of that, some requests/protocols may still send requests over your normal network instead of Tor, leaking your real location.
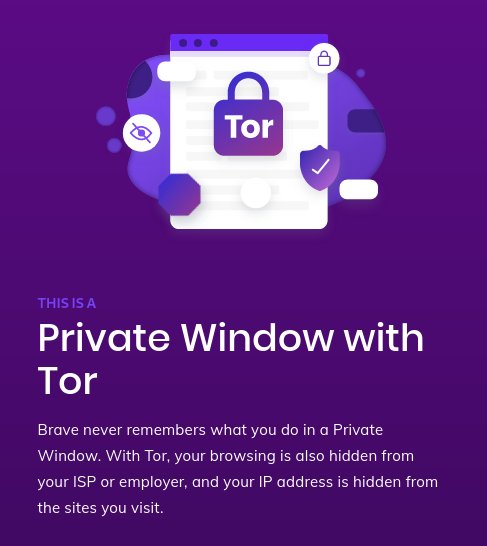
Users can leverage some of Tor's features in a special window in Brave.
Despite being built on top of Chrome’s source code, Brave has announced that it does not plan to adopt Google’s proposed change to how extensions function, leaving room for traditional ad blocking extensions.
Brave also comes with a cryptocurrency experiment, the Basic Attention Token (BAT) that allows users to pay content creators in micropayments, but despite it appearing prominently throughout the browser it is fully optional and can safely be ignored.
Chrome
Platforms: Windows, Mac, Linux, Android, iOS
Maintainer: Google
Chrome has been a pioneer in safeguarding users’ security. It was the first major browser to implement robust sandboxing, a method of reducing or nullifying the impact of security vulnerabilities exploited in a given browser tab, on all platforms.
Before using Chrome, you should consider whether Google is part of your threat model, given the company will be collecting some anonymized data about you as you browse the web, and can tie data to your Google account when logged into Chrome. If you’re already using some Google services like Gmail or Drive, then you may not be concerned with additional data collection.
Given that Google’s largest revenue source is advertisements based on tracking cookies, it’s no surprise that Chrome is lagging behind Firefox and Safari in blocking them. Google is phasing out the use of third-party cookies through 2023. For a few years, it was spearheading an effort to enable interest-based tracking of similar groups without the use of cookies — a scheme they call "Federated Learning of Cohorts." Following criticism from privacy and civil liberties organizations for enabling new and potentially more sweeping forms of behavioral targeting, Google is now experimenting with a newer series of interest-based categories they call Topics. According to Google, "Topics are kept for only three weeks and old topics are deleted. Topics are selected entirely on your device without involving any external servers, including Google servers. When you visit a participating site, Topics picks just three topics, one topic from each of the past three weeks, to share with the site and its advertising partners." Google says users can edit their topics, or disable this feature within settings.
Chrome also offers a “profile” feature, which allows you to build multiple profiles to compartmentalize different accounts and browsing activity (similar to Firefox’s containers).
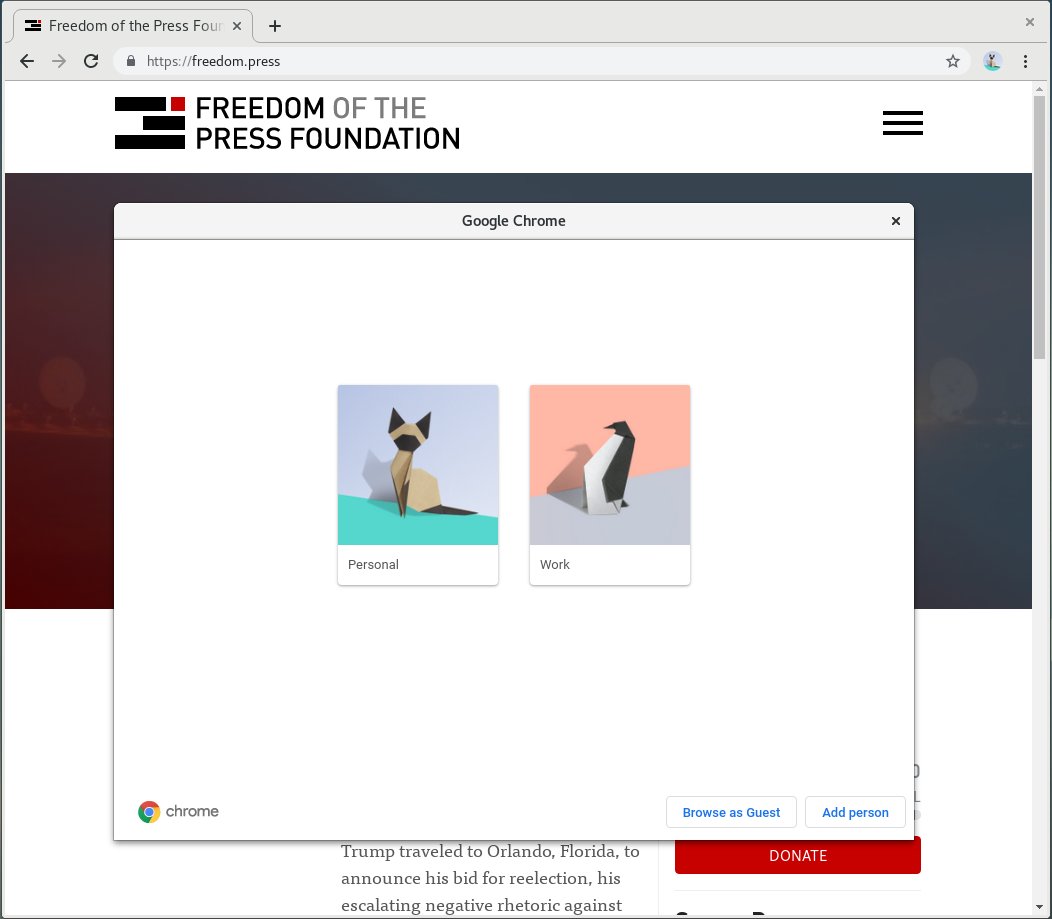
Users can easily switch between different "Profiles" on Chrome.
Chrome enables DNS-over-HTTPS if your system’s current DNS provider supports it. This aims to preserve users’ choices of DNS providers. While not enabled by default, users can also go into their privacy and security settings within Chrome, and manually change their DNS provider.
Users may want to enable extra extensions for stronger privacy, including uBlock Origin and the Electronic Frontier Foundation’ and Privacy Badger, or other ad/tracker blockers with access to even more tracker block lists.
Google has also begun rolling out its plan to scale back the permissions given to extensions by default. The Chrome team expects that this will help prevent malicious extensions from stealing your data, but it may also require authors of legitimate extensions to change how they work. Some of the newly proposed limitations are expected to limit the ability of many extensions — namely ad blockers like uBlock Origin — to perform effectively. It is now unclear whether Google will carve out exceptions for complex extensions (including adblockers), but if this extension functionality is important to you, it may be a reason to consider alternative browsers.
Comparison of features
These browsers all provide some similar privacy and security features, but may not be directly comparable. This table is intended to give a high-level comparison of all of the different features discussed above.
Legend:
- Yes - Enabled by default
- Available - Included in the browser, but disabled by default
- Partial - Not fully implemented
- Needs addon - Functionality is available through a third-party addon/extension
- No - Not included
| Tor Browser | Firefox | Brave | Chrome | ||
|---|---|---|---|---|---|
| Platforms | Desktop | Yes | Yes | Yes | Yes |
| Mobile | Android only[1] | Yes | Yes | Yes | |
| Network | Automatic HTTPS redirection | Yes | Yes | Yes | Yes |
| DNS-over-HTTPS | n/a, relies on Tor exit node to provide DNS | Yes for US users, available for others[2] | Partial[3] | Available[4] | |
| Tor integration | Yes | No | Partial[5] | No | |
| Privacy | Anti-fingerprinting measures | Yes | Available[6] | Yes | No |
| Blocklist for trackers | No[7] | Available[8] | Yes | Partial[9] | |
| Tracker blocking via third-party cookies | Yes | Yes | Yes | Partial[10] | |
| Distinct profiles | No | Yes | Yes | Yes | |
| Security | Sandboxing | Partial[11] | Partial[12] | Yes | Yes |
| FIDO2/U2F security keys | No | Yes | Yes | Yes | |
| Automatic updates | Yes | Yes | Yes | Yes | |
| User experience | Bookmarks & history | Partial[13] | Yes | Yes | Yes |
| Desktop/mobile sync | No data to sync, n/a | Yes | Yes | Yes | |
| Add-ons/Extensions | Not recommended[14] | Yes | Yes | Yes |




