When people ask us what messaging app is the best for them, we usually like to have a conversation about their specific privacy and security needs. However, when put on the spot to give one answer, in most cases we will encourage journalists to use Signal — particularly if they’re located in the United States.
Why is that?
Oftentimes people hear that a communications app is “end-to-end encrypted” and assume that means that it’s safe for communicating privately. But one of the most important properties of encrypted messengers is how they handle metadata, which can’t always be concealed with encryption.
What is metadata? This is information about your information. It’s basically anything other than the content.
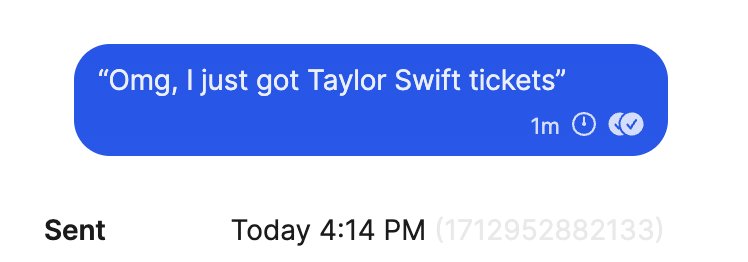
For example, in the above, the content is the message “Omg, I just got Taylor Swift tickets.” Meanwhile, the metadata could include:
- The sender of the message.
- The receiver of the message.
- The date the message was sent.
- The time the message was sent.
- The digital size of the message.
- The approximate location of the device that the message was sent from.
- The approximate location of the device that the message was delivered to.
This metadata may or may not be available to the people in the chat, but would be visible to the company that owns the messenger app (i.e., Meta or Apple) and that retains the metadata.
At Freedom of the Press Foundation, we generally urge you to use communications tools and apps that have a minimal amount of metadata retained by the app service provider. Let's walk through a few examples of why metadata matters.
WhatsApp, a communications app owned by Meta (formerly known as Facebook), uses the same end-to-end encryption protocol as the Signal app. However, the WhatsApp privacy policy makes clear that Meta stores information about your profile, your contacts, when you are using the app and for how long, who you’re chatting with, details about the type of device you’re using (including if your operating system is up-to-date and how charged your battery is!), your location, and more.
A 2021 ProPublica article noted, “Facebook Inc. has also downplayed how much data it collects from WhatsApp users, what it does with it and how much it shares with law enforcement authorities. For example, WhatsApp shares metadata, unencrypted records that can reveal a lot about a user’s activity, with law enforcement agencies such as the Department of Justice.” A Rolling Stone article from the same year confirmed this, reporting that the FBI could access this metadata in real time, with records being produced as often as every 15 minutes.
By contrast, the Signal privacy policy explains that the amount of metadata retained by the service is quite small. It includes your account creation date and the last time that you used the app. That’s it.
There is evidence of this working in practice. In 2016, The New York Times reported that although the U.S. Justice Department has also forced Signal to disclose data about its users, Signal “turned over the only pieces of data it could: the time the user’s account had been created and the last time it had connected to the service — far less than the government sought.” Despite this, governments continue to subpoena Signal for user data, yet receive almost nothing.
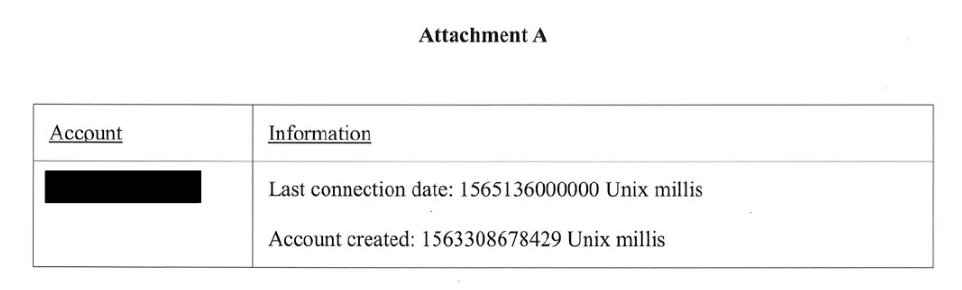
Caption: Screenshot of search warrant for Signal user data, Santa Clara County. Credit: Signal Foundation
You should assume that all of the major apps that you’re using are storing metadata about your communications and are receiving similar government subpoenas. We’ve covered the government’s propensity to use legal requests to access journalists’ information before and this behavior is unchanged. Apple, Google, Microsoft, Meta, and other tech companies all publish transparency reports showing not only government requests for information but also how often they comply with such requests.
Additionally, ordinary SMS text messages are not only vulnerable to legal requests but are perhaps the most risky of all, because they both lack end-to-end encryption and because they stockpile metadata with few safeguards.
So while minimal retention of metadata isn’t the only detail that journalists should consider when choosing how to communicate, it is a huge part of it. Companies that collect and store significant amounts of metadata create a large potential privacy risk for individuals using their platforms and apps.
What can you do?
- Use Signal, taking advantage of its advanced security features when needed.
- Protect your sources by ensuring that they can get you info in a way that minimizes potential government surveillance.
- If you have to use WhatsApp, please enhance your security settings around it — but be aware that the metadata is still going to be an issue. (Note that iMessage on iOS and Google Messages on Android will have some similar metadata issues to WhatsApp)
While this article goes into the basics of communications metadata, there’s even more to learn.
Read our short primer on media metadata or check out our more comprehensive guide: “Everything you wanted to know about media metadata, but were afraid to ask.”
Our digital security training team is also always ready to support news organizations who want assistance learning how to handle sensitive files. If you are a journalist in need, reach out to us!