Don't let email overwhelm you. The more you know about the privacy and security of email, the better off you and your sources will be. Photo by Xavier Verges. CC BY 2.0
For journalists, email is a ubiquitous form of communication. In the face of today’s proliferation of messaging platforms, email remains a common tool in every reporter’s repertoire. Of its many applications in newsmaking, email often plays an essential role in connecting journalists to their sources.
But just because email is one of the first ways a source might reach out, that doesn’t mean we should always use it. It doesn’t happen all the time, but sometimes we have sources who would be put at risk through the use of email.
There are plenty of other methods journalists use to communicate besides email. This is a toolkit that also features face-to-face meetings, postal mail, phone calls, and messaging apps. Using each form of communication carries with it its own upsides, and risks. Our goal in this piece is to contextualize some of the risks in using email, so that journalists are better positioned to leverage it in an informed and safe way.
Before potentially burning a source or tipping off a target before you're ready, journalists should know the privacy and security constraints of email — who can see your emails, and when? Consider carefully when it’s better to use encrypted alternatives, or to move off of email altogether.
To illustrate, let’s walk through some upsetting real-world examples.
Who can snoop on your emails?
The vast majority of email providers take steps to secure your email messages while they travel between your and your recipients’ inboxes. This method to safeguard data as it travels across the internet is called transit encryption. Transit encryption scrambles the content of messages so no one besides you, the person you’re contacting, and your respective email providers can read the message as it travels between inboxes. It’s a step in the right direction, but it won’t hide your email content from all parties along the way.
When you send an email, who’s sitting between your email provider (e.g., Google) and your recipient’s provider (e.g., Microsoft)?
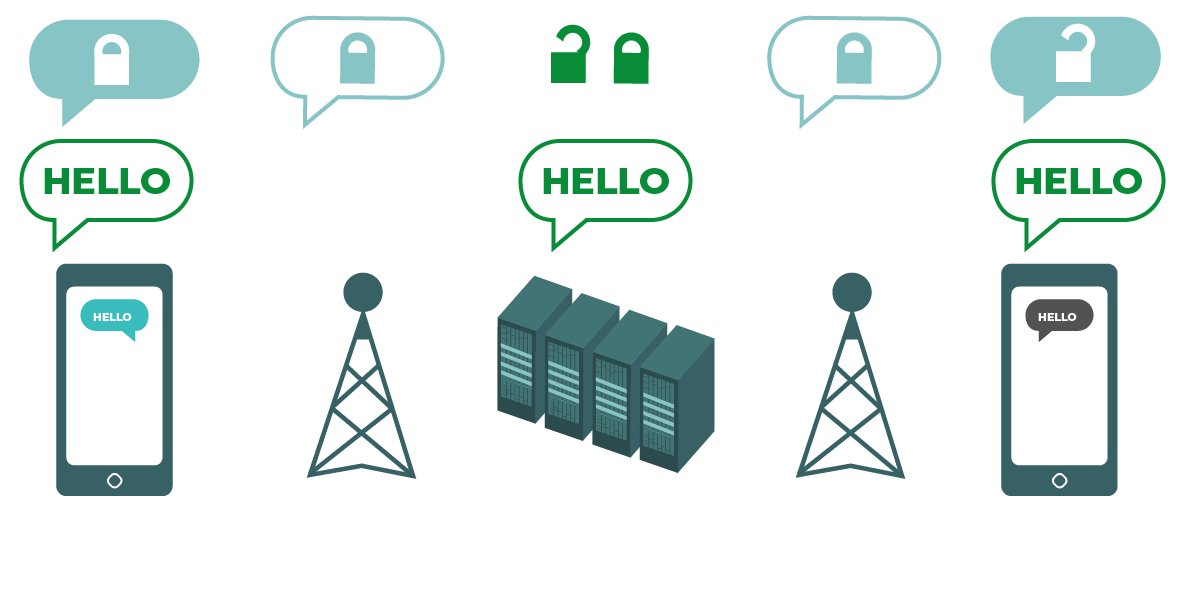
This graphic gives an example of how message content is protected as it travels between your and your recipient’s phones, through transit encryption. Source: Electronic Frontier Foundation
In the diagram above, the message content, “HELLO,” is available to you and your recipient (see: the phones on either end of the conversation), as well as the communications platform you’re speaking on (see: the computer servers in the middle). Thanks to transit encryption, no one else along the way (see: anyone monitoring the cell towers between the phones and the servers) can see the content of the message.
Even with transit encryption applied, your email message content may be accessed by the following parties:
- Your and your recipient’s email provider: e.g., Google for Gmail users, Microsoft for Office365 users
- Hackers with access to your or your recipient’s email account: e.g., hackers with your email account login information
- Legal authorities: e.g., courts, civil litigants, or U.S. agencies with the authority to compel you, or a company to disclose communications data.
- Your and your recipients’ email administrators: (e.g., anyone with administrative access to your workplace email), who may have extra privileges to audit your messages. This usually applies to email users with organization-provided email over cloud mail services (e.g., with G Suite), or local mail servers (e.g., Microsoft Exchange Server).
There have been many cases when journalists and their sources have been burned by email because of its exposure to all the above groups.
How exactly can someone get access to my email messages?
If an outside party—like a government or criminal entity—wants access to your email account, generally there are two ways in: a legal request to you or your email provider, or hacking into the account directly.
To use a non-technical example, think of your email inbox as your home. If someone wants to enter your home, they can do so by either: knocking on the front door (e.g. making a formal legal request to Google for your email records), or picking the lock to your back door (e.g., using your stolen login credentials from a known password dump).
The likelihood of such breaches really depends on who you are, where you are, your beat, and maybe even who your sources are. Not everyone is equally likely to be targeted, but as radically public figures, all journalists are far more likely to suffer these kinds of legal and extralegal breaches than the general public. Let’s talk through some real-world examples.
Knocking on the front door: Legal requests for email content
Legal requests targeting a journalist’s communications don’t happen every day, but they do happen.
We can call back to court-authorized surveillance measures that have caught journalists in their dragnet, raising debate amongst legal scholars and first amendment groups about their legality in the first place.
Generally in the U.S., courts are supposed to only grant a demand for a journalist’s communications content if there is probable cause a journalist has conspired, or co-conspired, in a crime. Authorities can get metadata with a lower burden of proof. A warrant isn’t required to produce metadata, just a subpoena or court order, which have been increasingly granted by courts in recent years.
We know there are always exceptions to the rule. While we are aware of some of the legal loopholes that law enforcement will use to degrade journalists’ protections, the legal landscape is constantly shifting.
In the long run, it benefits your storytelling and your source’s privilege to err on the side of caution when it comes to the use of email when reporting.
Unfortunately this is not a hypothetical.
Case study: A legal request for communication content

Journalist David Sanger’s reporting in the New York Times kicked off an FBI investigation to identify his source. Source: Center for American Progress
In 2012, the New York Times published an excerpt from journalist David Sanger’s soon-to-be published book. The report detailed classified US intelligence operations, and set off an FBI investigation into the source of the leak.
Sanger, along with journalists at several other outlets, published details about a project responsible for inflicting severe damage on Iran’s nuclear program, purportedly through the use of Stuxnet malware jointly developed by the U.S. and Israel.
During the course of the probe, the content in emails between the alleged source of the leak, retired General James Cartwright, and numerous reporters were submitted into evidence — along with other data, including email and phone records.
What legal measures did FBI investigators use to obtain journalists’ email messages?
According to the warrant issued to Google requesting Cartwright’s email content, no journalist email accounts were directly targeted in legal requests. But, a message always has a sender and a recipient. Investigators didn’t have to issue separate legal orders for the journalists involved in Cartwright’s case in order to read the content of their messages. Instead, all investigators had to do was gather enough evidence to seize the messages from the other end of the conversation: Cartwright’s email account.
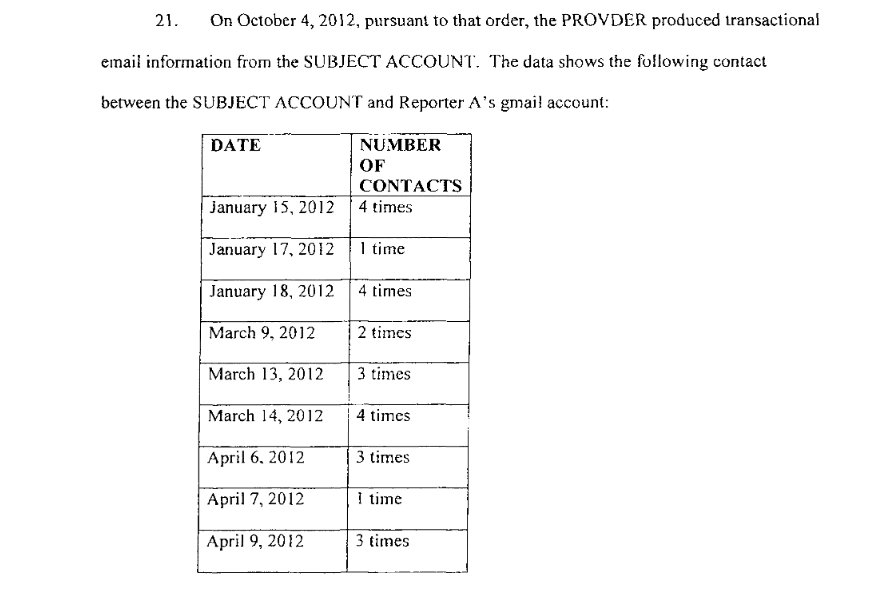
In court documents supporting a warrant for Cartwright’s emails, FBI investigators list email metadata previously acquired from Cartwright’s Gmail account (“SUBJECT ACCOUNT”). Source: U.S. District Court for the District of Columbia
Before issuing a warrant for the content of messages in Cartwright’s Gmail inbox, investigators acquired email metadata through a previous request to Google. Listed as evidence for probable cause in the warrant excerpt above, that same email metadata demonstrates that Cartwright was in contact with Sanger (“Reporter A”) numerous times over the four months leading up to Sanger’s reporting on Stuxnet.
In recreating a conversation history between a journalist and a suspected source, investigators gave the court justification to pry further into Cartwright’s private Gmail messages with journalists. And, with that, the court agreed the FBI had enough evidence to merit seizure of his email content.
This excerpt from the warrant requesting Cartwright’s draws out the investigatory scope of the seizure. Source: U.S. District Court for the District of Columbia
In 2016, Cartwright was charged with a felony count of lying to FBI investigators. He was later pardoned by President Obama shortly before he left office in 2017.
This case study bears an important lesson: Even when doing the best you can to keep your communications private, your entire conversation runs the risk of falling into the wrong hands if it’s available to outside parties, or even if some parts of the conversation happen over the channels you don’t control.
What’s more, this lesson rings true when reporting on topics beyond national security. For example, many corporate email environments are set up so that email administrators have deep insight into the messages employees send and receive. What this means is that if a source who reaches out to a journalist on their work email, they may have also exposed that message to their company’s email administrator. In an age when both government and corporate entities are cracking down on leaks, knowing who can tune into either end of a conversation is essential for privacy.
We wrote more about the Sanger case, and the surveillance capacity of some corporate email administrators, in the context of the use of Google’s G Suite. If you use G Suite in your newsroom, or communicate with someone who does, read all about its privacy and security properties.
Knocking on the front door: Legal requests for email metadata
Requests for non-content communications records (which we sometimes call message metadata) generally require a much lower threshold to obtain in criminal and civil cases involving journalists’ electronic communications records. In the U.S., both warrants and subpoenas can be used to compel a journalist, or a communications provider, to submit email records as evidence.
Email metadata — information about the message, such as what time an email was sent, its recipient, and its subject line — can be just as revealing as the content of messages.
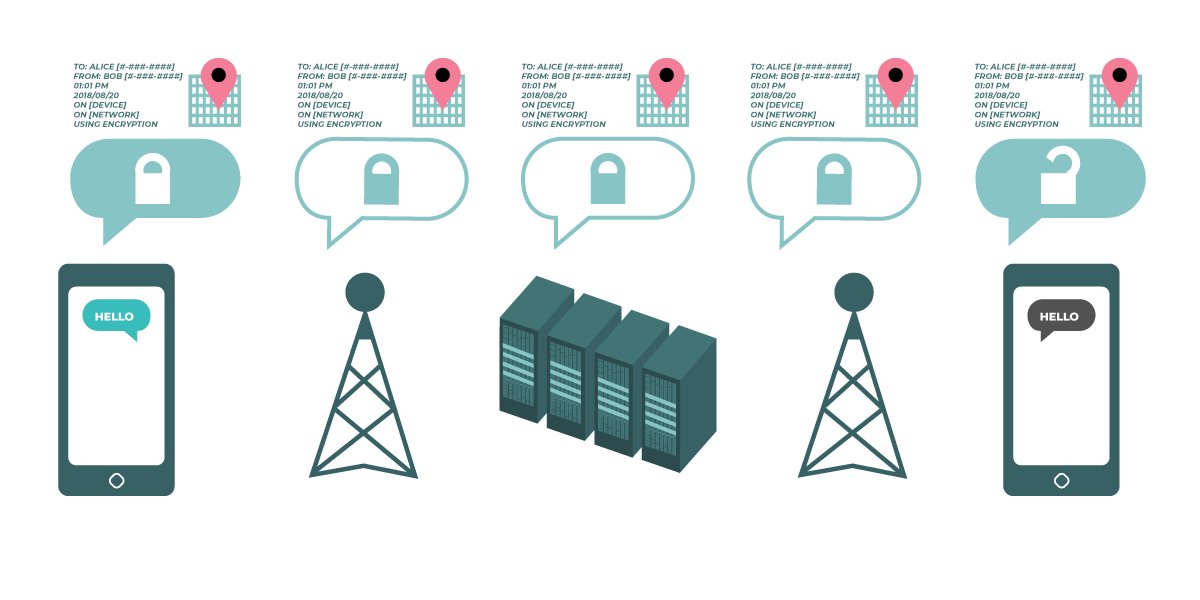
This graphic demonstrates that even with encryption applied to protect the content of a message, its metadata is still available as it travels from point to point between your and your recipient’s phones. Source: Electronic Frontier Foundation
By comparing the message history between two email accounts against key events in a leak investigation, prosecutors might have just enough data to reconstruct the relationship between a journalist and potential sources.
Case study: A journalist’s email metadata obtained in a leak investigation, without her knowledge
In 2021, following revelations that the Department of Justice under Trump targeted several journalists in secret requests for phone and email records, Attorney General Merrick Garland published a memorandum strictly limiting the circumstances under which the Department can make records seizures of the press:
In this context, records seizures are defined as: legal requests (subpoenas, court orders, or warrants) targeting journalists, newsrooms, or third-party service providers (e.g., Google, Facebook, Dropbox) for, “testimony, physical documents, telephone records, metadata, or digital content.”
Formally approved as policy in July 2021, the new guidelines state that the DoJ will not seize journalists' records so long as they are, “acting within the scope of newsgathering activities.” In other words, members of the press have a reasonable expectation that their records will not be seized during a leak investigation, even if they possess and report on classified government documents.
Of course, there are several exceptions to these new DoJ protections. The DoJ maintains the right to seize records if a journalist violates criminal law in the process of procuring government documents (e.g. by breaking and entering), or if a journalist is under investigation for a crime, presumably outside of their journalistic duties, like insider trading.
As an added check against the DoJ investigatory powers, the updated rules require the Attorney General to personally provide "advance approval" on all records seizures of journalists, sealed or otherwise. Though press freedom organizations welcome the new rules, DoJ guidelines don’t have the force of law, so the Department can potentially break them without any accountability. We are hopeful these updated guidelines will provide stronger protections, but recent history suggests the press should not place confidence in the DoJ to be its own referee.
The 2021 rules expand on prior 2015 DoJ guidelines, which were themselves a response to public outrage about DoJ overreach in two-high profile leak investigations (AP journalists, and former Fox correspondent Jay Rosen). Under the 2015 guidelines, with approval from the Attorney General, records seizures could be made without any notice to the journalists or news organization in question.
Despite these modest limitations on journalists’ communication records, the public learned that DoJ investigators took sweeping opportunities to keep journalists in the dark during leak investigations. Let’s look into a recent example of where a reporter had their email metadata spied on, despite the existence of these supposed rules.

Ali Watkins covered national security with several publications between 2014 and 2017, the period for which the DoJ requested her email records. Source: Twitter/@aliwatkins
Without her knowledge at the time, the DoJ obtained years of New York Times journalist Ali Watkins’ email records. The aim of the request was to gather evidence against now-retired Senate Intelligence Committee aide James Wolfe, who was suspected of leaking classified information to Watkins and other journalists.
In June 2017, the DoJ indicted Wolfe for lying to FBI investigators about his contact with journalists, as well as lying about sharing classified information with Watkins and another journalist. In December 2017, he was charged on three counts of lying to investigators and sentenced to two months in prison. Wolfe was never charged with the crime of leaking classified information to the press, the very question at the heart of the probe.
In February 2018, months after Wolfe was indicted, Watkins received a letter from the DoJ, alerting her that roughly three years’ of metadata from two personal email accounts and a phone number were targeted as part of the investigation into Wolfe.
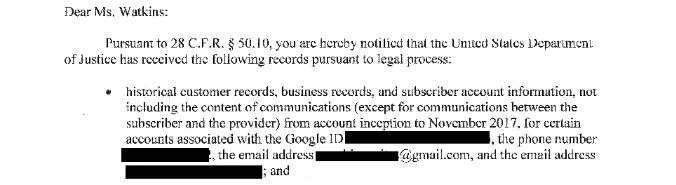
An excerpt of the letter the DoJ sent to Watkin's, which specifies the scope of what was seized from her email accounts and phone records. Source: Reporter’s Committee for Freedom of the Press
In an excerpt from the notification letter sent to Watkins above, we see the scope of the request, covering communications metadata sent from both email accounts “from account inception to November 2017.”
During this period, Watkins covered national security at a number of outlets. She maintains Wolfe was never a confidential source in any of her reporting. What’s more, Wolfe was never charged with the crime of leaking classified information to the press.
This case highlights a couple worries about the liability email can pose to journalism.
First, the sheer volume of Watkins’ personal email metadata swept up into evidence is dizzying. The DoJ seized communications metadata from two email accounts, calling for historical details of who she emailed and when, between the creation of each account and November 2017. These records likely involve countless people unrelated to the initial investigation. Paired with her phone records, which were also seized in the inquiry, investigators could have a highly detailed view into years of her journalistic work, and personal life.
Second, Watkins had no opportunity to oppose the legal order for her records before the request was granted by her email provider. Without forewarning, journalists are denied the opportunity to seek legal counsel and fight requests for their communications data. This poses serious risks to ongoing journalistic investigations, and any sources implicated in such a request. It also means that we can’t know who is looking at our emails, and we can’t assume our emails will be kept private.
Picking the lock on the back door: Email account hacking
What if the attacker doesn’t have leverage over, or care about, the legal process?
Email hacking campaigns can originate from many different sources (e.g., state intelligence agencies, state-sponsored contractors, independent hacktivist groups) and leverage various technical methods (e.g., account phishing, computer surveillance malware), but they all aim to accomplish the goal of getting direct access to a target’s email inbox.
Once a hacker can access your email account, they typically have the same capabilities as you: They can view and export the contents of your inbox, change your login information to lock you out of your account, send emails masquerading as you, log in to other accounts that use your email account for recovery purposes, and so on.
A hacked email is a jumping-off point for additional attacks; this is why it’s so important to protect these accounts from hacking.
Case study: Hacking group gains access to journalists’ email inboxes
In 2014, the Syrian Electronic Army (SEA) hacking group appears to have launched a politically-motivated attack on Forbes. Through a series of spearphishing emails sent to Forbes employees, the SEA was able to gain administrator access to Forbes’ Wordpress CMS, deface the Forbes website, publish defamatory posts, and harvest a database of Forbes usernames, emails, passwords, which they published online.
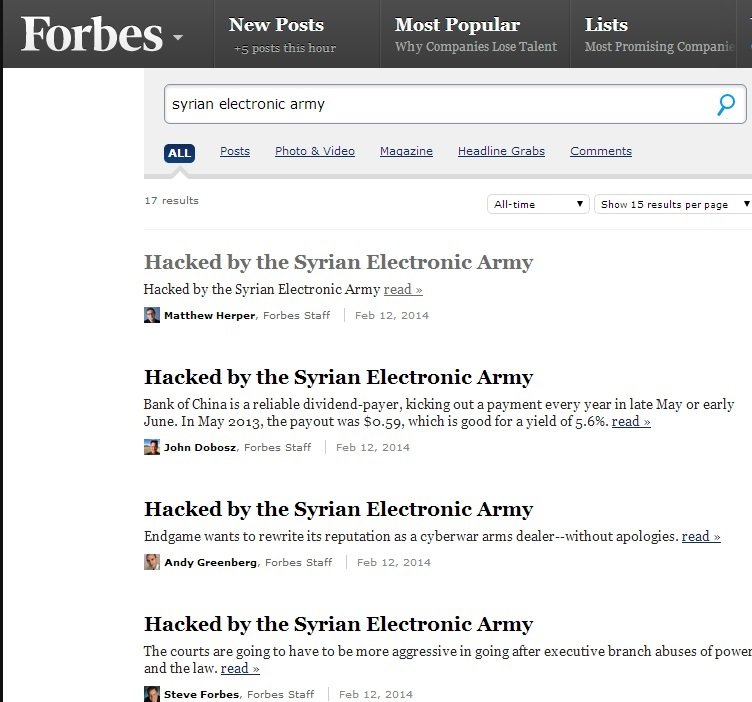
SEA operatives edited several recently published posts to Forbes’ blog with the title, “Hacked by the Syrian Electronic Army.” Source: thehackernews.com
How were these hackers able to cause such damage?
The attack was choreographed in stages, and after examination, Forbes’ technical staff suspect that momentary, unauthorized access to a Forbes email inbox proved to be a valuable asset over the subsequent stages of the campaign. With a Forbes staffer’s email username and password harvested from a fake login page, SEA had just enough time to change the user’s WordPress password with the “forgot password” email function common to most online platforms.
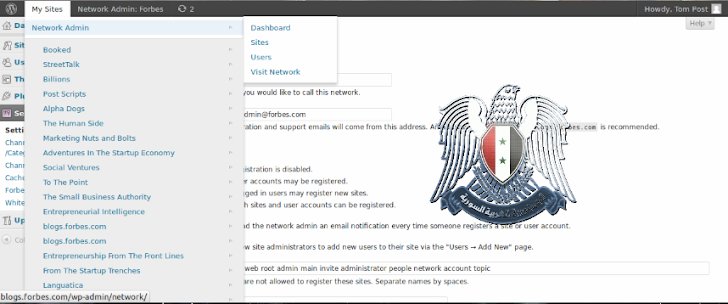
SEA tweeted an announcement of their successful operation with this screenshot of Forbes’ admin portal on their WordPress CMS backend, complete with an SEA logo watermark. Source: thehackernews.com
From there, they logged into Forbes’ Wordpress, and leveraged the user’s administrative privileges to change the emails and passwords of various accounts to ones controlled by the hackers. While not technically advanced, this stage gained the hackers more time to act while Forbes played hacking-whack-a-mole.
Spearphishing attacks, which leverage information an attacker knows about a target in the hope that they will give up valuable information like a username and password, are extremely common. Generally, all it takes is one person to click on the wrong link, download the wrong attachment, or sign in on the wrong page for a spearphishing attack to succeed.
Most spearphishing attacks can be prevented, however, with one added security measure: Two-factor authentication (2FA). When you enable 2FA on an account like your email, anyone trying to sign in with your credentials will only be able to do so if they have your username, password, and two-factor authentication code, which you typically get on your phone as a text or through an app. So long as an attacker doesn’t have access to your phone (save a few exceptions), they won’t be able to get into your account — because they have no way to get the 2FA code accessible only through your phone.
Nobody wants to get “got”
The will of political leadership to eavesdrop on journalists’ communications is always in flux. The Obama administration charged more sources and journalists under the Espionage Act than all previous administrations combined. Under Trump's presidency, the DoJ pursued a record number of leak investigations.
While the Biden Administration's public messaging signals a positive swing towards more journalist protections in leak investigations, members of the press have learned to take a wait-and-see approach, all while doing their best to proactively protect their sources. Journalists must consider the likelihood that their email records may be scooped up in legal requests, and the possible harms to their newsroom and sources if their records are given up.
Beyond the legal apparatus, many corporations have deep visibility into their employees’ communications, in part to prevent and investigate leaks to the press.
If you’re worried about legal requests for your email content or metadata...
Before using traditional email to communicate about an investigation, check if your email provider offers a transparency report (e.g., Google, Microsoft). Platform providers publish transparency reports to share data with their users about the number of legal requests they’ve received from government and civil entities, and the amount of data they’ve produced per request (e.g., no data, metadata-only, or content and metadata).
Oftentimes, the data is organized by country. If you’re worried about a particular legal authority making requests about your email messages, you can do specialized research into how your (and your recipient’s) email provider has responded to that authority in the past. Ultimately, you want to make an informed decision before trusting an email provider with your valuable communication data.
If you’re worried about hacking into your email account...
Spearphishing attacks targeting journalists’ email accounts will likely continue to be a favorite tactic of dedicated hackers. Learn how to spot and avoid phishing attempts, and lock down your accounts with a strong and unique password (ideally generated by a password manager) and two factor authentication (preferably through a mobile app like Google’s Authenticator or Twilio’s Authy). If you want advanced help protecting highly-sensitive accounts, contact our trainers.
And, if the stakes are too high...
If using traditional email is too risky for a given investigation or conversation, take it to an end-to-end encrypted platform, which will only allow your messages to be read by the intended recipient. With end-to-end encryption, not even the service provider can read your messages. If it’s appropriate for your situation, we have guides on using end-to-end encryption over email with Mailvelope and ProtonMail.
But better yet, don’t use email at all when you're looking for confidentiality. Email encryption can be complicated and doesn’t protect the metadata, which might expose you regardless of whether or not you do it right. Move away from email altogether with an end-to-end encrypted messaging app like Signal or more anonymous methods like SecureDrop.
Whether they’re knocking on your front door or picking the lock to your back door, some actors will go to great lengths to figure out what you’re saying and who you’re saying it to. Now that you know the methods these actors may use, take a moment to determine whether email is the best way forward with a source or a colleague — before you click “send.”