Also available in Spanish.
The encrypted messaging app, Signal, has become a newsroom staple for communicating with sources, accepting tips, and talking to colleagues. While it’s a practical tool for anyone concerned with the security and privacy of their conversations, journalists are particularly interesting targets and would benefit from locking down Signal.
(If you’re not yet using it, learn how to get started here.)
Signal makes it easy to have a secure conversation: It looks and feels identical to your default text messaging app, but security experts so often recommend it because of what it does in the background.
Signal offers end-to-end encryption, meaning only conversational participants can read the messages. While regular phone calls or text messages allow your phone company to unscramble your conversations, even the team behind Signal can’t listen to them.
You don’t need to take their word for it. Signal is open source, meaning the code is available for anyone to review, and security audit specialists have torn it apart and confirmed as much. Signal retains nearly no metadata, or information about who spoke to whom and when. (The developers proved it in court.)
These are advantages you want in an encrypted messaging app. Newsrooms can attract unwanted attention, and journalists who already use Signal should consider hardening it against physical access, unwanted remote access, and network-based eavesdropping. Here’s how:
Remote access and network eavesdropping
Confirm your connection security with safety numbers
Signal, unlike most messaging apps, allows you to verify that your session is encrypted to the right person and not an eavesdropping third party. To confirm your connection, open up a conversation with someone you want to talk to and look for their “safety numbers.”
iPhone users: Press your partner’s name (at the top of the screen) > View Safety Number
Android users: Press your partner’s name (at the top of the screen) > View Safety Number
You’ll see your safety numbers and a QR code. If you and your contact are together in person, press “scan code” on the safety number screen and use your camera to scan their QR code. If you are not together, we suggest verifying your safety numbers on a different platform where you feel confident you’re talking to the right person.
If you both see the same numbers, your session is secure — go ahead and mark each other as “verified.” If the numbers don’t match, you shouldn’t talk over this channel.
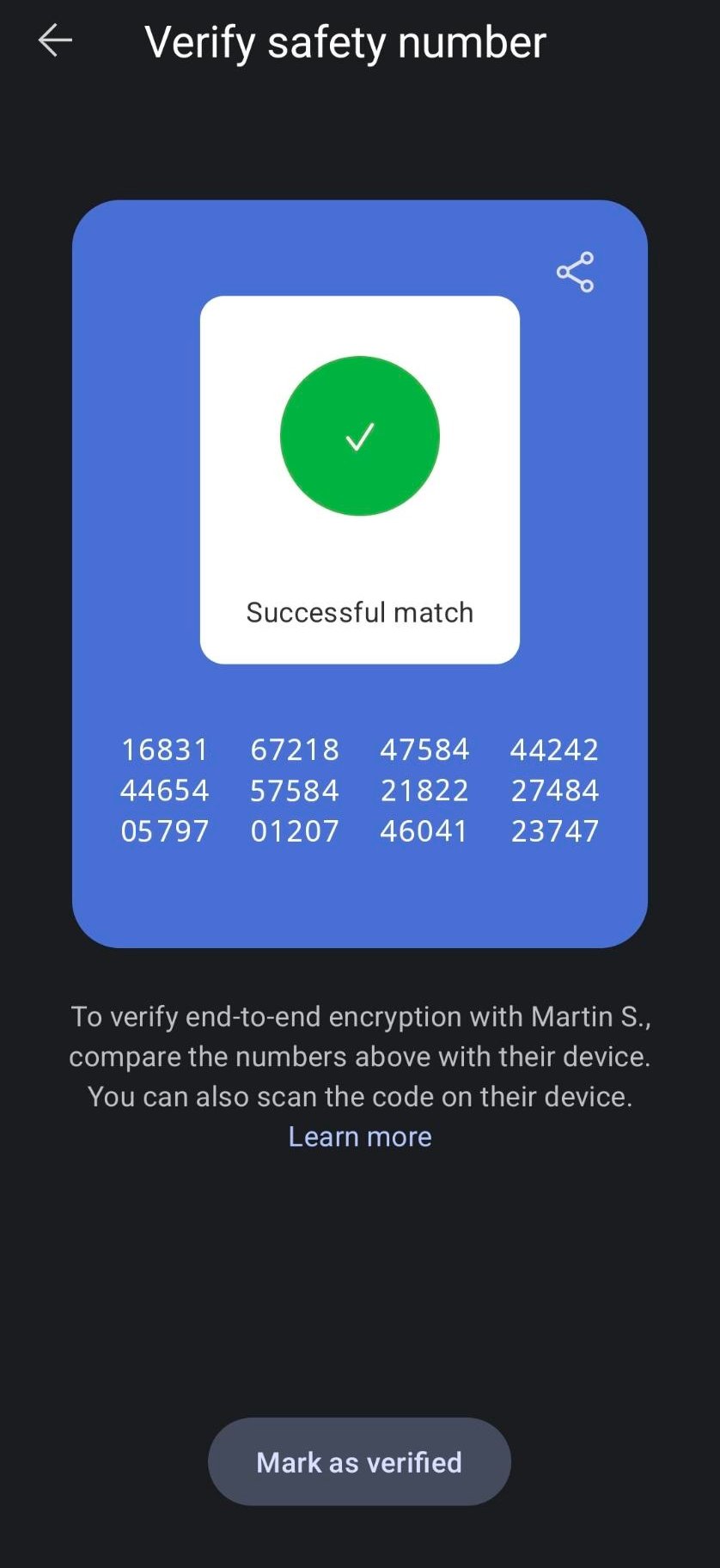
You won’t need to verify safety numbers again until someone resets the session, like when they get a new phone.
If safety numbers do change, Signal will send a notification. If this happens, use another channel to verify the session is secured before you continue communicating sensitive information.
Keep your phone number more private
If you want to hand out an identifier besides your phone number so people can reach you, you’ll need to set up a username. If you haven’t set this up already, you can enable a username here:
iPhone users: Press Settings (profile icon at top left) > [Your name at the top of the screen] > Username
Android users: Press Settings (profile icon at top left) > [Your name at the top of the screen] > Username
You can also prevent people from looking you up by your phone number if desired.
iPhone users: Press Settings (profile icon at top left) > Privacy > Who can find me by number > Nobody
Android users: Press Settings (profile icon at top left) > Privacy > Who can find me by number > Nobody
On this screen, you’ll also see an option to allow contacts to see your phone number. We recommend leaving this set to “Nobody.” It’s important to note that contacts who have previously had your phone number may still be able to see it (e.g., via their contacts app).
iPhone users: Press Settings (profile icon at top left) > Privacy > Who can see my phone number > Nobody
Android users: Press Settings (profile icon at top left) > Privacy > Who can see my phone number > Nobody
Registration lock with PIN
Use Registration Lock to lock in your Signal number.
iPhone users: Press Settings > Account > Registration Lock > Enabled
Android users: Press Settings > Account > Registration Lock > Enabled
Your account is protected by a PIN. This PIN will prevent your number from being re-registered from a different device, so write it down or keep it somewhere safe. This might be a physically hidden notebook or password management software.
By default, you are offered a short numeric PIN, but you can make it stronger by using a PIN that also enables text beyond the phone number.
iPhone users: Press Settings > Account > Change your PIN > Create alphanumeric PIN
Android users: Press Settings > Account > Change your PIN > Create alphanumeric PIN
Signal will occasionally nudge you with a prompt to re-enter your PIN to ensure you still remember it.
Disable link previews
Signal offers the ability to retrieve previews of webpages linked within a conversation. According to the developers, when this feature is enabled Signal makes direct requests to websites to generate these previews. In other words, link previews leak the websites you share in your conversation to those websites.
Confirm link previews are disabled.
iPhone users: Press Settings > Chats > Generate link previews > Disabled
Android users: Press Settings > Chats > Generate link previews > Disabled
Don't leak keyboard data
Many phones come with multiple keyboards for different languages and functionalities, and allow you to download customized keyboards. This can be useful, but keyboards can share data with third parties. For example, Google’s keyboard is enabled by default on many Android devices, and unless you customize your keyboard settings, you may unknowingly save keyboard data beyond Signal.
Android users should enable the “Incognito” keyboard in Signal.
Android users: Settings > Privacy > Incognito keyboard > Enabled
Beyond Signal, your choice of keyboard can affect your privacy so make sure you know which keyboard(s) you have enabled.
iPhone users: Settings app > General > Keyboards
Android users (may be slightly different, depending on your version): Settings app> General management > Language and input > On-screen keyboard
iOS users: Keep your Signal history off iCloud
If you use iCloud and you don’t want to share call history on Signal — including who spoke to whom, when, and the call length — confirm it’s turned off here: Settings > Privacy > Show Calls in Recents > Disabled.
Why you want disappearing messages
While Signal lets you delete individual messages, these messages will only be deleted on your device. Instead, use Signal’s “disappearing messages” feature to remove messages from a conversation automatically, after a time amount of your choosing. This is particularly important for journalists concerned about messages on a source’s phone.
To turn on disappearing messages, first open a conversation.
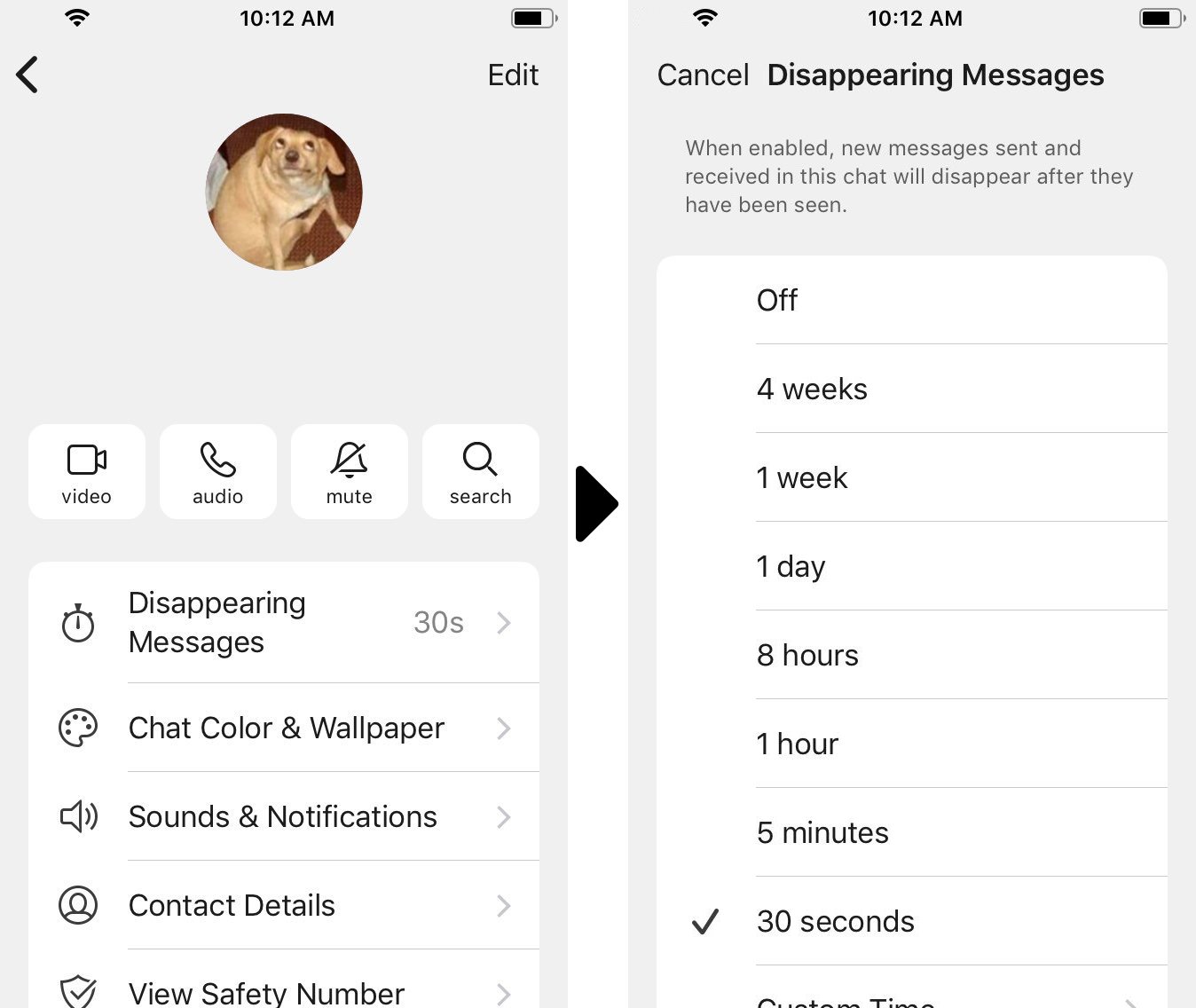
iPhone users: Press on your partner's name at the top of the screen to open the settings menu for this conversation. Press "Disappearing Messages."
Android users: Press on your partner's name at the top of the screen to open the settings menu for this conversation. Press "Disappearing Messages."
Set the amount of time you'd like to keep the messages, between 30 seconds to four weeks, or a custom time of your choice. This works both for one-on-one conversations and group chats.
You can also set a default message disappearance time for new conversations.
iPhone users: Settings > Privacy > Default timer for new chats
Android users: Settings > Privacy > Default timer for new chats
Messages you've sent or received before enabling disappearing messages will still be there. If you want those to disappear, you will need to manually delete them.
Device security
The weak points in end-to-end encrypted conversations are the “ends” — the physical devices where the messages arrive in human-readable text. There are a few things you can do to lock down your devices.
Password protect your device
Encryption won’t help with someone who gets access to your unlocked phone, so you’ll want to password-protect your device. Exit Signal and turn on a passcode.
iPhone users: Settings app > Face / Touch ID & Passcode
Android users: Settings app > Security > Screen lock
Consider turning on screen lock

Unlocking your phone also means decrypting your messages. You can require one additional step to re-enter your password before unlocking Signal.
It doesn’t happen every day, but unlocked phones are stolen in plain sight — while walking down the street or on the train. Likewise, maybe you allow your son or daughter to entertain themselves on your phone, but you don’t want them to see photos from your source.
iPhone users: Press Settings > Privacy > Screen Lock
Android users: Press Settings > Privacy > Screen Lock
Turn on disk encryption
If your phone is ever lost, stolen, or seized, it’s possible to copy and read any data on the device, including your encrypted messages. The good news: You can easily protect your device with disk encryption.
If you use a modern iPhone, congratulations! Your device is already encrypted.
Modern Android devices are encrypted by default (e.g., Pixel and Samsung Galaxy lines). Check your Android system settings for disk encryption to make sure disk encryption is enabled. If not, setting up disk encryption is easy.
Hide screen in app switcher
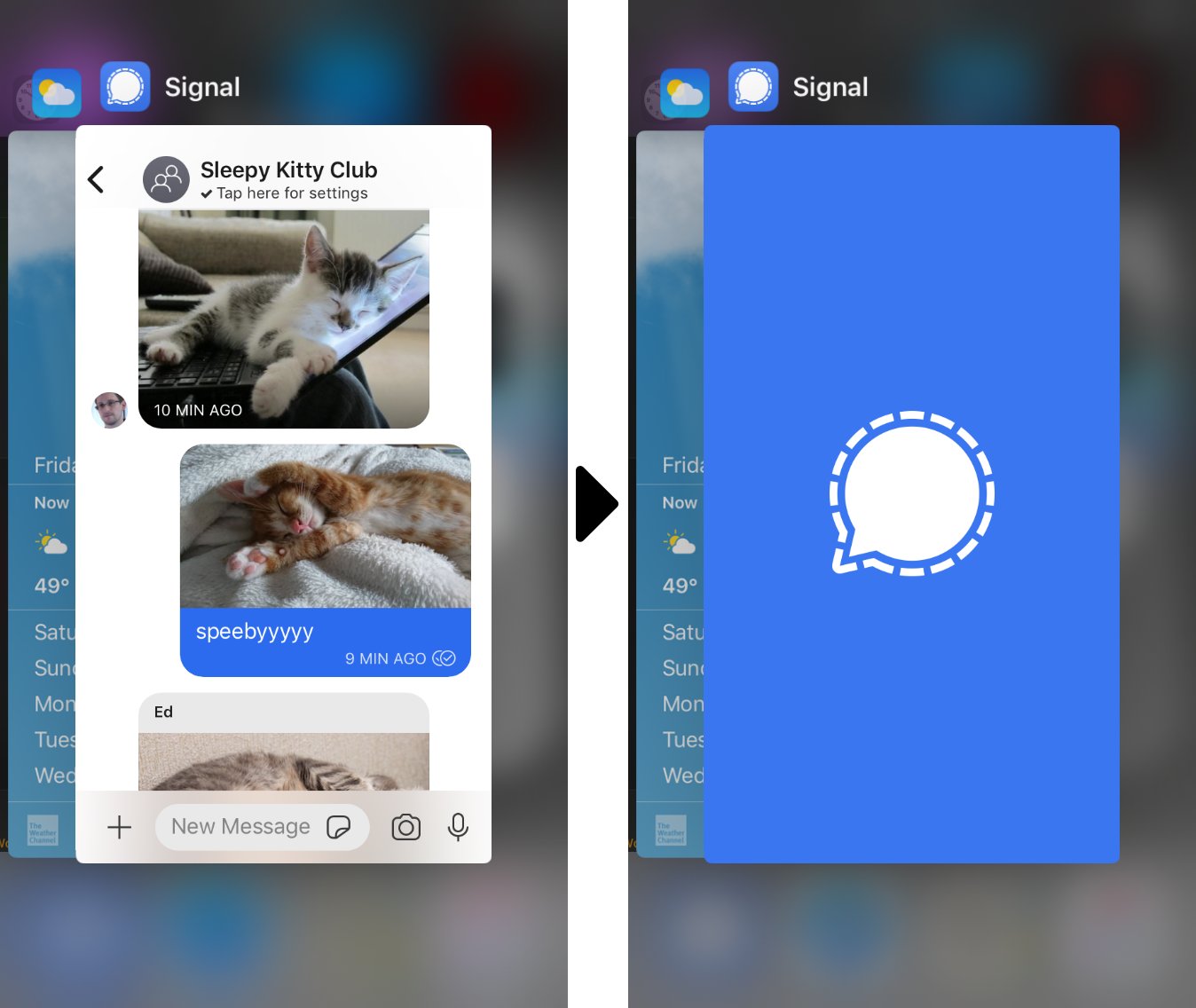
Signal gives you the option to prevent a preview from being shown in your app switcher, unless you explicitly open the app.
iPhone users: Press Settings > Privacy > Hide Screen in App Switcher
Android users: Press Settings > Privacy > Screen Security
Notification privacy
Even when your phone is locked with a password, anyone who picks it up can still read the message and sender name from your lock screen.
iPhone users: Settings > Notifications > Show. To receive notifications with no information about the sender or the content of your messages, turn on “No Name or Content.”
Android users: Settings > Notifications > Show. To receive notifications with no information about the sender or content, press “No name or message.”
Updates and defending against malware
Many types of malware are designed to send screenshots of your messages, or recordings of conversations, to a remote hacker. The single best thing you can do is stay on top of software updates, which usually include security patches for your operating system, Signal, and any other apps you have. Older devices that no longer receive security updates are at the greatest risk.
Safest choice: Only use your mobile device
Signal offers a desktop application, but it's safer to keep your messages only on your mobile device. Desktop devices typically allow applications to talk to one another. Android or iOS devices deliberately isolate apps, requiring strict permissions for what data can be accessed and when. Malware has a significantly more difficult time compromising your data on an updated mobile device.
Know the limits of end-to-end encryption
- For a security win, use Signal only on mobile and lock down your device. But there are drawbacks if you lose your phone or need to purchase a new one. While the registration lock feature prevents others from taking your Signal number, it would also prevent you from being able to re-register your number.
- Signal isn't designed to protect against live metadata surveillance, so it doesn’t protect your identity or the identity of anyone you talk to. It's best to assume you are identifiable to other Signal users.
- Even if you’re practicing great security hygiene, your conversational partner can put your messages at risk if they are not being careful. Encourage others to lock down Signal as well.
For news organizations looking for more hands-on assistance with encrypted messaging tools and practices, please contact us about our training options. If Signal is a service you value, consider donating to support their work.